Software supply chain security
Keep your applications clear from malicious software packages throughout the full software development lifecycle.
Challenges
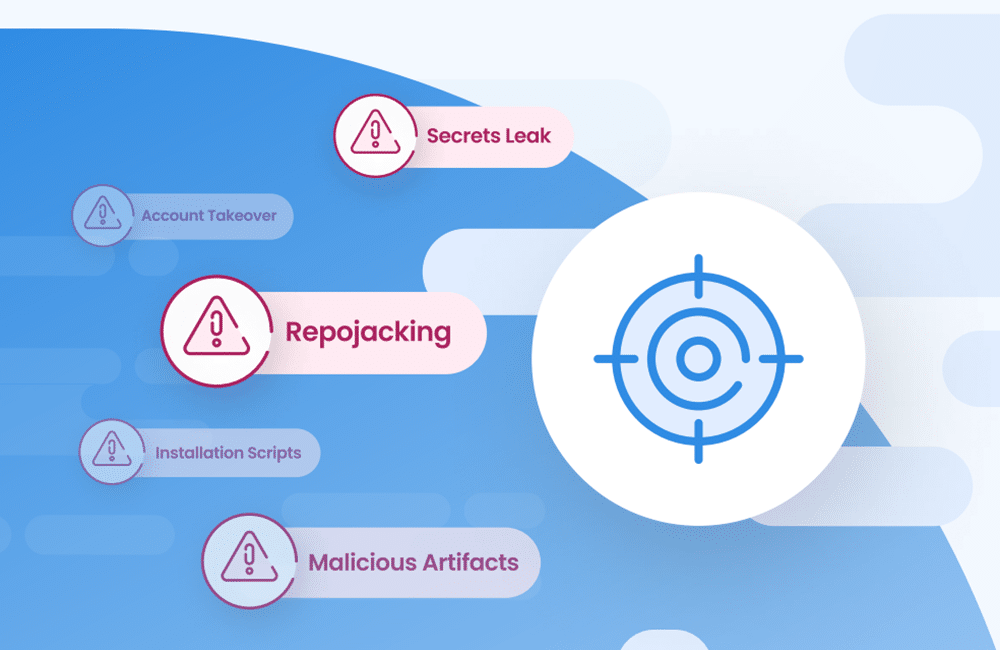
Active threats lurk in libraries
The open source packages developers rely on to get their work done also make great hiding places for bad actors seeking to cause damage to enterprise organizations.
Supply chain malware
Hackers inject malicious code into open source packages to quickly introduce vulnerabilities into tens of thousands of open source dependencies.
No time to scan
Regular code scans take time that developers often don’t have, meaning many weaknesses are accidentally missed.
The race to keep up
Open source packages are frequently updated, making it incredibly difficult for companies to stay on top of all vulnerabilities across different versions.
Opportunities
Stop supply chain threats
Prioritize and automate to secure code, protect users, and stop malicious actors in their tracks.
Integrate. Automate.
Built-in tools that find and block malicious packages like protestware, data stealers, and crypto miners reduce enterprise risk.
Centralize visibility and control
Broad coverage of repositories, CI/CD pipelines, and beyond stops malicious packages and vulnerabilities from slipping in.
Keep up with dependency updates
The key to staying a step ahead of malicious packages or exploitable vulnerabilities is automatically ensure all dependencies are kept up to date.
The solution
Find and block threats across the SDLC
Mend SCA protects repositories, CI/CD pipelines, and beyond from malicious code packages and exploitable vulnerabilities.