Leave no container unturned
Analyze the contents of container images to identify security vulnerabilities ahead of deployment – and address potential risks.
Challenges
More abstraction. Less time.
Cloud-native development brings new potential risks—and at the same time, adds another level of abstraction between the security team and the code. But while application security complexity has increased, development schedules have shrunk.
Fast vs. Secure
Staying on top of vulnerabilities buried deep across multiple containers is a huge challenge. And with frequent updates and deployments, it’s nearly impossible to keep up, let alone get ahead, of security risks.
High volume overload
The sheer volume of images and dependencies takes far too long to scan. And when everything is shipped at speed, vulnerabilities can easily slip through.
Dependency neglect
Open source libraries and packages incorporated in containers rarely get checked for dependency updates, which means that external risks may be skipped over.
Opportunities
Cut through container complexity
Simplifying container security starts by giving time back to security teams, getting them actionable insights quickly, knowing which vulnerabilities to prioritize and which pose no threat, and building a clear view across the SDLC.
Gain a clear view across the SDLC
Leveraging container security and SCA in tandem cover everything from single images to entire registries.
Quickly know what matters
Container-level reachability and runtime monitoring quickly identify what risks are exploitable and what can be safely ignored.
Keep your secrets safe
Discover unprotected sensitive information before malicious actors do.
The solution
Mend AppSec
Development to deployment coverage for cloud-native applications
From scanning images and K8s to secrets handling and reachability analysis, the platform helps you identify and remediate vulnerabilities – before and after deployment.
Discover Mend AppSec
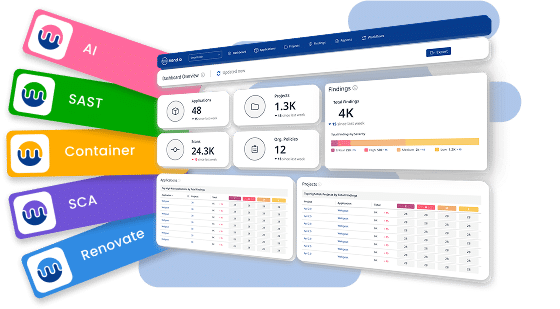
Stop managing alerts.
Start reducing risk.
Join the teams reducing remediation effort by 75%.