Table of contents
Welcome to Mend, Diffend!

Today we’re thrilled to announce that Diffend, an innovative software supply chain security service, is now part of Mend.
At Mend we believe that open source risk management is a pillar of software supply chain security, and Diffend helps us extend our capabilities in this area. While 99.999% of open source releases may be safe, our customers trust us to help identify the ones that could do harm and should be avoided. Enter Diffend.io: an industry-leading tool with several innovative features.
The last year has shown that malicious actors will go to great lengths to compromise software supply chains, and open source risks need to be kept in check. We know that burying our heads in the sand and never updating a dependency out of fear is not a viable strategy, especially considering that pretty much every software development outfit regularly starts new projects with latest versions of open source dependencies anyway. Companies with critical projects depending on open source need a solution they can trust to deeply evaluate open source package risk and steer them clear of it.
What is software supply chain security?
Software supply chain security is a trending term in software development circles lately, for unfortunate reasons. If you think of a company’s traditional physical supply chain, for many it might take an Oceans 11-style scheme to penetrate and exploit. Software, on the other hand, which almost every company in the world today needs to build in some form, has many avenues of penetration which are difficult to secure.
Although the SolarWinds hack did not directly involve open source, it’s the most widely known instance of software supply chain security. Attackers gained access to a build system, used that to compromise published software, and then were able to use this to compromise over 100 other large companies who were users of the software, plus multiple government agencies.
Supply chain incidents haven’t stopped there. Just last week, the popular code coverage company Codecov disclosed that attackers had compromised one of their install scripts, which in turn could have been used to exploit many of Codecov’s 10’s of thousands of users.
These incidents show a trend where attackers target components of a company’s software supply chain to gain access and then leverage such access for greater gain — causing greater damage to the unfortunate victims.
Software supply chain security and open source
There’s no debate that securing open source is an essential part of securing the software supply chain. Research has shown that most software projects are comprised of 60%-90% open source in the final product, which is a large potential attack surface. But more importantly, open source software has much less inherent protection to begin with. It’s great that there’s no gatekeeping around who can publish open source, but our risk management needs to be calibrated accordingly.
Why Diffend.io?
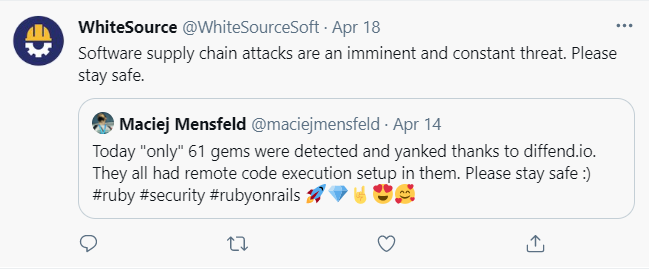
At Mend we look at open source risk holistically rather than purely from a security perspective. In 2020 we launched Merge Confidence, which reduces the risk of unintentionally “breaking” updates in open source, which is more common by occurrence, but thankfully much less impactful than a malicious act. When evaluating our progress towards automatically detecting and blocking malicious dependency updates, we quickly realized that Diffend.io was far ahead of the industry, thanks to the tremendous foresight of its founder Maciej Mensfeld and his successful collaboration with Tomasz Pajor.
In fact, since its public launch in early 2020, Diffend’s combination of automatic scanning with a system that flags packages for review hasn’t missed a single known malicious package on the Rubygems registry, and has been directly responsible for the majority of such packages being “yanked”, which in turn protects and entire community. Just last week, Diffend helped detect and remove 60 packages from Rubygems which were posing as innocent “security research” like Dependency Confusion, but actually opening up malicious backdoor capabilities.
A few more examples of Diffend’s innovative capabilities and ability to plan for future threats:
- Diffend detected and blocked the Dependency Confusion research gems months before this research was made public.
- Diffend was already built with capabilities to address Dependency Confusion directly by specifying private dependency patterns which should never be downloaded from the public registry.
- Diffend even has capabilities to detect and alert when dependencies in production get “yanked” from the registry. Diffend users were warned within 15 minutes of the mimemagic incident earlier this month.
Diffend and Mend
We’re especially happy to not only have acquired Diffend but also to have its Founder Maciej Mensfeld join our team as Senior Product Manager for Supply Chain Security. Maciej’s vision in creating Diffend and foreseeing these types of security risks has been unparalleled. We’re excited to have him join to expand Diffend’s capabilities cross-language as well as integrate Diffend data and capabilities into Mend’s enterprise open source security capabilities.
Existing Diffend capabilities will remain free, so you are encouraged to sign up and create a free account so that you can be the first to know about the new languages and capabilities we will be rapidly adding throughout 2021. All capabilities will also be integrated into Mend’s Enterprise product range, including our advanced reporting and policy controls.
Welcome Diffend, and welcome Maciej!






