Table of contents
Best Software Composition Analysis Providers: Top 5 in 2026
What are software composition analysis providers?
Major software composition analysis (SCA) providers include Mend, Black Duck (Synopsys), and Veracode. They offer solutions to find, manage, and fix vulnerabilities and license issues in open-source components, with options ranging from developer-focused tools to enterprise-grade platforms with SBOM generation and deep compliance features.
These providers not only enumerate components but also analyze associated risks, such as security vulnerabilities, licensing issues, and code quality problems. Their offerings often integrate into the development pipeline, providing automated processes to alert teams about potential risks in real-time. This allows organizations to act quickly, reducing the chances of security breaches or legal complications stemming from unaddressed third-party code.
Key capabilities of SCA solutions:
- Vulnerability detection: Finds known vulnerabilities (CVEs) in open-source packages.
- License compliance: Checks for license conflicts and adherence to policies.
- SBOM generation: Creates Software Bill of Materials (SBOMs) for supply chain transparency.
- Exploitability analysis: Identifies truly exploitable vulnerabilities.
- Malware detection: Some tools offer behavior-based malware detection.
Key capabilities of SCA providers
Vulnerability detection
Vulnerability detection is at the core of any SCA provider’s functionality. These platforms maintain extensive databases of known vulnerabilities (such as CVEs) and cross-reference the identified components in a project against this data. When a match is found, the system alerts users to the presence of vulnerabilities, typically including severity metadata and references for further investigation. This capability allows organizations to identify security flaws early.
Proactive vulnerability detection is not simply about identification; it’s also about reducing the window of risk exposure. Continuous scanning enables immediate detection of emerging threats, supporting timely remediation within the software lifecycle. Since new vulnerabilities are discovered regularly, frequent scans and automated alerts keep development teams informed and enable quick responses to newly surfaced security issues.
License compliance
SCA tools provide license compliance analysis by detecting and categorizing the licensing terms of all identified software components. Most open-source libraries come with specific obligations, and using them incorrectly can expose organizations to legal and financial risks. SCA providers help organizations track which licenses are in use, determine compatibility, and flag components with restrictive or unknown licenses.
Managing license compliance is about more than avoiding legal trouble; it also supports policy enforcement and risk management. Development teams can set license usage policies within the SCA tool and receive automated notifications when a library doesn’t match allowed criteria. This process reduces manual effort in legal reviews, helps with due diligence during M&A, and ensures ongoing software compliance across all releases.
Open source licensing in 2026 is complex
Most teams don’t know where their exposure lives until it’s a legal problem. This guide shows you exactly where to look.
SBOM generation
Software bill of materials (SBOM) generation is a key feature in modern SCA offerings. An SBOM is a machine-readable inventory that details every component, dependency, and version present in an application. SCA tools can automatically produce SBOMs during the build process, providing a reliable source of truth for internal security reviews and regulatory compliance. Industry standards such as SPDX and CycloneDX are usually supported for interoperability.
SBOMs are increasingly important for supply chain transparency and risk assessment. Regulatory bodies and enterprise customers are beginning to mandate SBOMs as part of their procurement and vendor risk processes. By automating the creation and upkeep of SBOMs, SCA providers help teams comply with evolving industry standards, facilitate audits, and accelerate incident response when new threats are discovered.
Exploitability analysis
Exploitability analysis moves beyond basic vulnerability identification by assessing whether a discovered vulnerability is actually reachable or exploitable within the application’s context. SCA providers may utilize techniques, such as call graph analysis or runtime instrumentation, to determine whether the affected code paths are invoked under normal or expected workflows. This distinction helps security teams prioritize issues by risk, reducing alert fatigue and focusing remediation efforts where they matter most.
Contextual exploitability analysis helps organizations avoid over-prioritizing theoretical risks that don’t pose a practical threat. By integrating exploitability insights, SCA tools provide actionable intelligence, the difference between a long static list of vulnerabilities and a prioritized queue of real risks. As a result, remediation resources are channeled more effectively and software risk is more accurately managed.
Malware detection
Some SCA providers incorporate malware detection to check third-party and open-source components for signs of malicious code or tampering. This may involve both static and dynamic analysis, scanning for signatures of known malware or behaviors indicative of supply chain attacks. As common software supply chain attacks often inject malicious code into otherwise trusted libraries, this capability is increasingly vital.
Beyond known malware signatures, advanced SCA solutions may leverage heuristic or behavioral analysis to detect suspicious activity within dependencies. Rapid identification of malware-laden or backdoored packages enables organizations to react swiftly, prevent deployment of compromised software, and maintain the integrity of their development lifecycle. This layer of defense supplements traditional vulnerability and license scanning by protecting against an evolving threat landscape.
Related content: Read our guide to software composition analysis tools
Notable software composition analysis providers
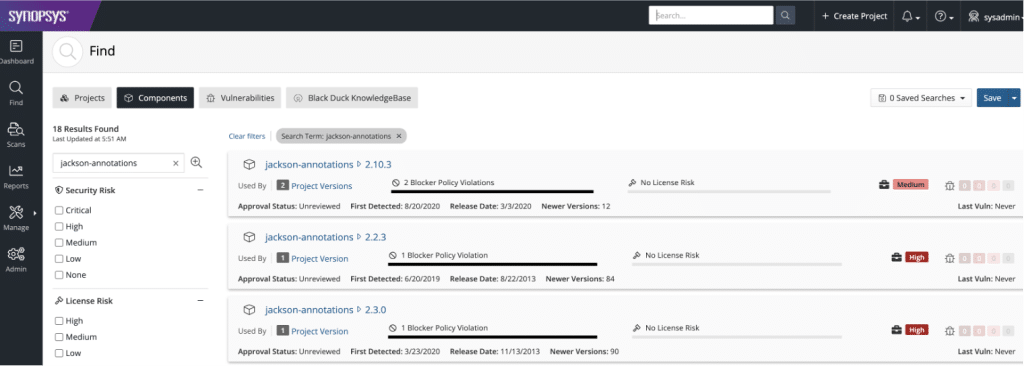
Black Duck SCA

Black Duck SCA by Synopsys is a software composition analysis solution to identify and manage security, license, and quality risks in open-source and third-party components. It supports multiple scanning methods (source, binary, codeprint, and snippet analysis) to provide broad and deep visibility into software dependencies.
Key features include:
- Multi-method scanning: Detects dependencies through source code, binaries, file system analysis, and code snippets, enabling full coverage even without source code access
- Dependency analysis: Identifies both direct and transitive dependencies, offering complete insight into open-source usage
- Security advisories: Provides vulnerability data with risk context to prioritize remediation
- Policy enforcement: Allows teams to define and automatically enforce open-source usage policies across the SDLC
- SBOM generation: Supports creation of industry-standard SBOMs for regulatory compliance and customer assurance
Veracode SCA

Veracode software composition analysis helps teams detect and remediate risks in open-source components with high precision and low false positives. It integrates directly into development environments, enabling immediate scanning and auto-remediation without disrupting workflows. By leveraging a proprietary vulnerability database that goes beyond the National Vulnerability Database (NVD), Veracode provides early visibility into emerging threats.
Key features include:
- Fast onboarding and scanning: Enables teams to set up and scan in development environments with minimal effort
- Auto-remediation: Automatically suggests accurate fixes for license and vulnerability risks, reducing time to resolution
- Proprietary vulnerability database: Detects known and emerging risks not yet published in the NVD, improving threat coverage
- Prioritized risk insights: Helps teams focus on the most critical issues with contextual risk data and ultra-low false positives
- Integrated policy and governance: Enforces open-source usage policies and helps avoid compliance penalties through automation
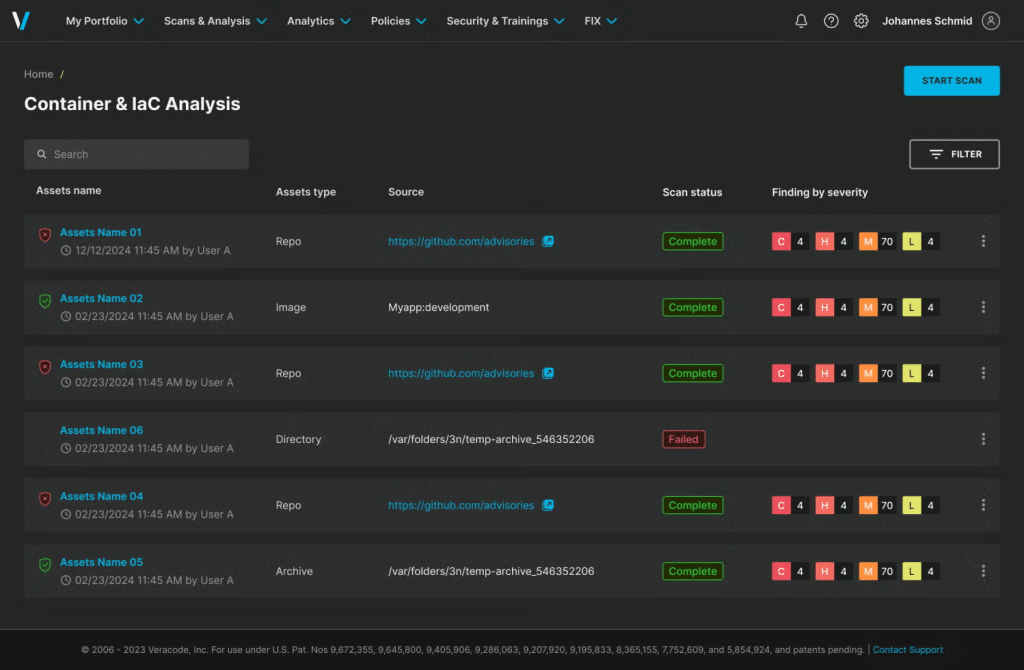
Source: Veracode
Checkmarx SCA

Checkmarx software composition analysis, part of the Checkmarx One platform, offers an accurate and automated solution for identifying and mitigating open-source risks across the software development lifecycle. It scans for vulnerabilities, license risks, and malicious packages while also providing reachability analysis to reduce noise and prioritize real threats.
Key features include:
- Industry-leading accuracy: Delivers near-zero false positives, outperforming competitors in third-party benchmarks
- Transitive dependency scanning: Detects indirect dependencies that may introduce hidden risks
- Malicious package detection: Identifies tampered or harmful packages introduced through the software supply chain
- Reachability analysis: Assesses whether vulnerable code is actually exploitable, helping teams focus on real risks
- Actionable remediation guidance: Offers clear steps to resolve issues, streamlining developer efforts
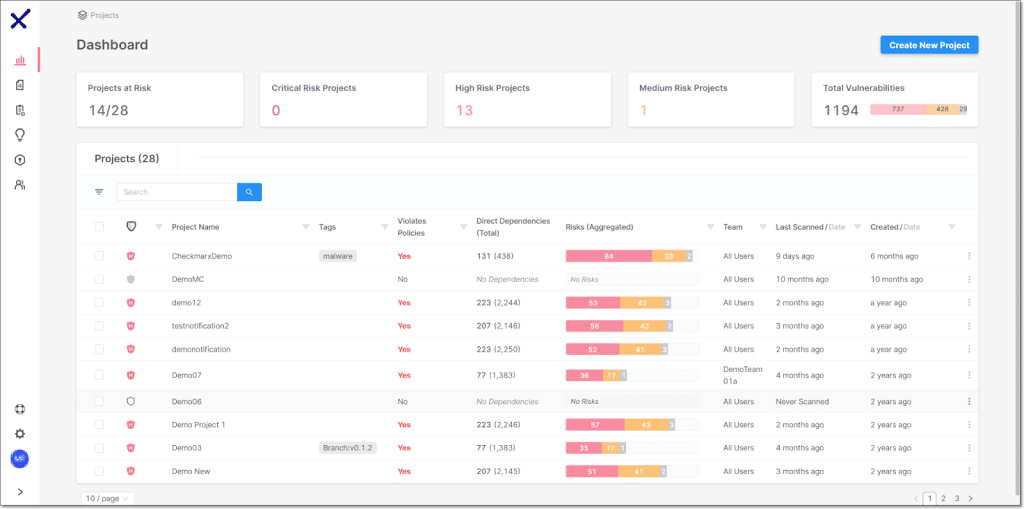
Source: CheckMarx
Sonatype SCA

Sonatype Lifecycle is a software composition analysis tool to automate the identification and remediation of open-source risks—helping teams manage vulnerabilities, license issues, and architectural concerns without disrupting development workflows. Backed by Sonatype's proprietary intelligence, it provides precise, low-noise results and integrates directly into developer tools and pipelines.
Key features include:
- Automated dependency management: Continuously monitors and manages open-source components across the SDLC
- Golden pull requests: Delivers pre-tested, automated remediation that resolves issues without breaking builds
- Contextual risk prioritization: Flags the most impactful vulnerabilities based on application context
- Flexible policy engine: Enables teams to define and enforce security and license rules across all projects
- Instant visibility: Dashboards provide real-time insights into risk posture and component health
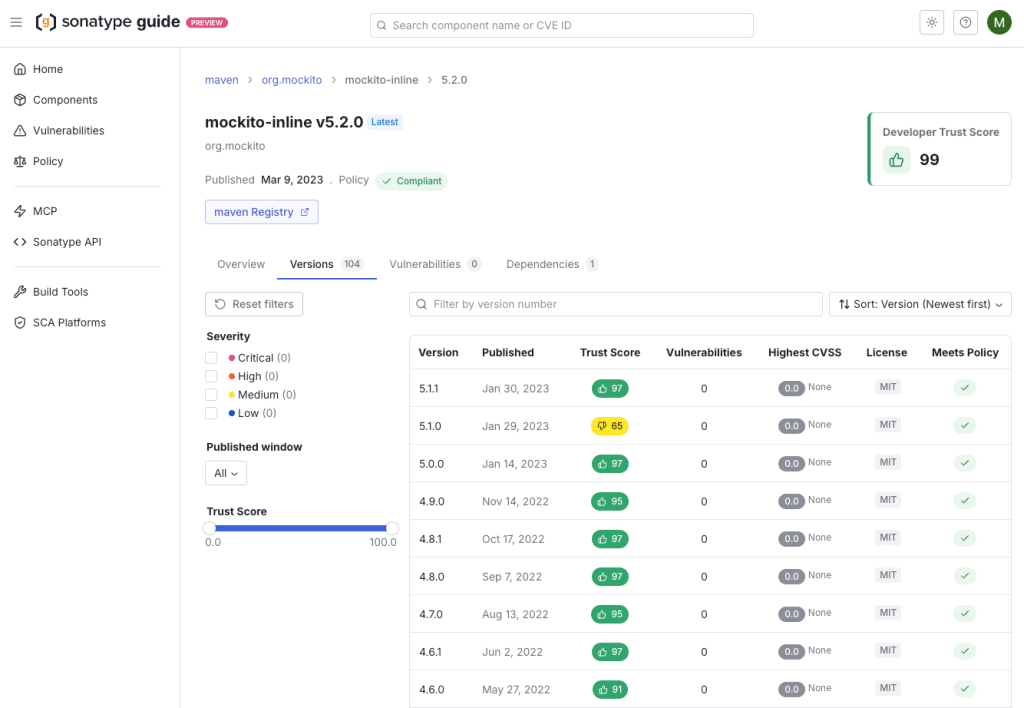
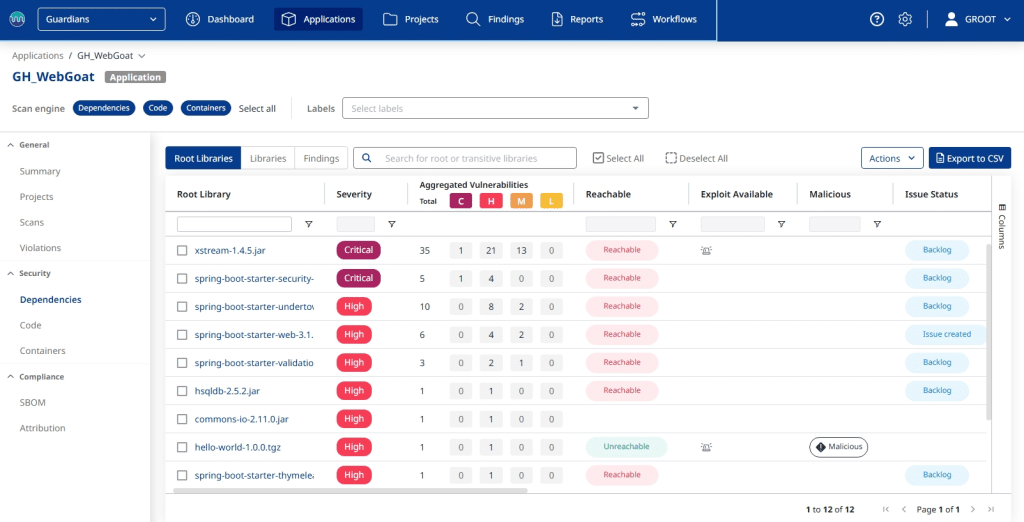
Source: Sonatype
Mend.io
Mend SCA is part of the Mend.io AI-native application security platform, helping organizations identify, prioritize, and remediate risks in open-source dependencies. It provides deep visibility into the entire software supply chain while integrating seamlessly into development workflows. Mend combines software composition analysis with automated remediation and AI-driven security capabilities to help teams secure modern applications, including those built with AI-generated code.
Unlike standalone SCA tools, Mend provides a unified platform that includes SCA, SAST, container security, automated dependency updates, and AI security capabilities under a single pricing model. This approach enables organizations to manage application security holistically while improving remediation efficiency and developer productivity.
Key features include:
- Automated dependency updates: Mend Renovate automatically generates pull requests to update vulnerable dependencies, enabling teams to remediate risks quickly without manual effort.
- AI security capabilities: Mend AI detects AI components in code, provides risk insights, improves system prompts, applies security policies, and enables AI red teaming for AI-powered applications.
- Fast remediation workflows: Automated remediation and developer-friendly workflows help organizations reduce vulnerability remediation time by up to 80%, significantly improving developer productivity.
- Comprehensive application security coverage: Combines SCA, SAST, container security, dependency updates, and AI security into a unified platform for full visibility across the application stack.
- Enterprise-scale ROI: Organizations using Mend typically reduce security risk exposure by 70–80% while saving $21M+ annually through automation and streamlined remediation processes.
Related content: Read our guide to SCA solutions
How to choose SCA providers
1. Accuracy and vulnerability coverage
Accuracy and vulnerability coverage are essential when evaluating SCA providers. The quality of an SCA tool’s vulnerability database determines the likelihood of detecting both well-known and newly disclosed risks. Providers must offer regular updates and extensive data sources, aggregating vulnerability information from public listings, private research, and affected vendor advisories. Without high accuracy, organizations risk false positives and overlooked vulnerabilities.
Another aspect to consider is how efficiently the provider correlates discovered vulnerabilities to the actual dependencies in use. Some SCA solutions invest heavily in reducing noise through matching algorithms and context-aware filtering, increasing trust in their findings. The right provider should balance breadth of coverage and precision of detection, ensuring that developers receive reliable feedback that won’t overburden them with irrelevant alerts.
2. Language and ecosystem support
Language and ecosystem support can make or break an SCA deployment for organizations that use diverse technologies. Tools must support all relevant languages, package managers, and environments present in the development lifecycle. This includes modern application stacks (such as JavaScript, Python, Java, and .NET) and legacy or niche technologies where older vulnerabilities still pose risks.
Effective SCA providers continually expand their coverage to reflect new frameworks and package repositories, adapting as development practices evolve. When selecting a provider, it is vital to validate their compatibility not only with current projects but also with potential future technology choices. This foresight ensures that SCA remains valuable and does not require replacement or manual workarounds as your technology landscape evolves.
3. Integration with your SDLC
Integration with the software development lifecycle (SDLC) is a must-have for modern SCA tools. The best providers offer plugins and APIs that connect directly to source code repositories, build tools, CI/CD platforms, and issue trackers. This enables automated component discovery and risk alerts at every stage, from initial commit to deployment. Tight integration eliminates manual overhead and ensures that SCA insights reach developers when they’re most actionable.
Automated integration also supports continuous security practices, enforcing SCA policies and monitoring without slowing delivery. Look for providers whose solutions can deliver near-real-time results, support gated pipelines, and trigger workflow automation in the tools your teams already use. This approach maximizes adoption, drives timely remediation, and fits naturally into an organization’s existing processes.
4. Actionable remediation guidance
Providing actionable remediation guidance is a differentiator among SCA vendors. It’s not enough to identify risks; tools must also help teams understand what actions to take—such as upgrading to a safe version or applying a workaround. Leading SCA solutions provide contextual recommendations, references to advisories, and links to patched releases or relevant documentation.
An advanced SCA provider may automate some remediations, generating pull requests or patches to address vulnerabilities with minimal developer intervention. This streamlines the process, reduces human error, and accelerates time to resolution. Good remediation guidance helps organizations prioritize and fix risks efficiently, supporting both security outcomes and developer productivity.
5. Performance and scalability
Performance and scalability determine whether an SCA tool can keep pace with your organization’s growth and workflow demands. Large codebases, frequent builds, and high developer activity can strain poorly performing tools. Look for vendors that demonstrate fast scan times, low resource overhead, and the ability to handle enterprise-scale repositories without dropping accuracy or coverage.
Scalability also involves handling concurrent projects, diverse teams, and reporting needs across distributed organizations. The best providers invest in infrastructure and optimization to ensure that SCA doesn’t become a productivity bottleneck. As your use of open source expands, a scalable SCA solution will support consistent, reliable security assessments, regardless of development velocity or project size.
6. Developer experience
Developer experience is a key consideration when selecting an SCA provider. Tools must offer clear, actionable feedback that integrates with the environments and workflows developers use daily—such as IDEs, version control systems, and collaboration platforms. Overly complex interfaces, noisy alerts, or rigid workflows can discourage adoption and reduce the effectiveness of the SCA process.
Best-in-class SCA solutions are designed with developer usability in mind. This includes features like rich contextual information, minimal disruption to coding, customizable alerts, and quick access to remediation. A positive developer experience increases engagement with security findings, improves adoption rates, and ensures that SCA adds value without slowing down delivery.
Conclusion
Choosing the right software composition analysis provider is critical for managing the security and legal risks of using open-source components. Effective SCA tools combine high vulnerability detection accuracy, strong ecosystem support, seamless SDLC integration, and actionable remediation guidance. As software supply chain threats increase and regulatory pressures mount, organizations must invest in scalable, developer-friendly SCA solutions to maintain trust, protect users, and ensure compliance throughout their software lifecycle.