Table of contents
Best Software Composition Analysis for Enterprise: Top 8 in 2026
What is software composition analysis and how is it used in the enterprise?
Software composition analysis (SCA) is an automated security practice that scans applications to find, track, and manage open-source/third-party components. It can identify security vulnerabilities (CVEs) and license compliance issues, create Software Bills of Materials (SBOMs), and enable “shift-left” security by integrating into DevOps pipelines to protect the software supply chain.
In a large enterprise, software composition analysis plays a central role in managing the scale and complexity of open-source usage across diverse teams and applications. With hundreds or thousands of services relying on third-party components, SCA enables centralized visibility, governance, and control over open-source dependencies. It supports security and compliance functions by enforcing policy across the organization, integrating with enterprise tooling like CI/CD platforms, artifact repositories, and ticketing systems.
Key functions of SCA for the enterprise:
- Inventory & bill of materials (SBOM): Automatically discovers all open-source components, their versions, and dependencies, generating a comprehensive inventory (SBOM).
- Vulnerability management: Scans components against vulnerability databases (like CVEs) to find known security flaws, prioritizing them by severity.
- License compliance: Checks for license obligations, ensuring adherence to legal requirements for open-source usage.
- Risk assessment: Assesses overall risk from components and suggests remediation, like upgrading to secure versions.
- Developer integration: Provides feedback directly within developer tools (IDEs, CI/CD pipelines) for early detection and resolution (Shift Left).
Why enterprises rely on software composition analysis
As software development increasingly depends on open source, enterprises need tools to manage the risks that come with third-party components. Software composition analysis provides that control. Here’s why it has become a critical part of enterprise application security and compliance programs:
- Visibility into open source usage: SCA tools generate a complete inventory of all open-source components, including transitive dependencies, allowing teams to know exactly what’s in their codebase.
- Vulnerability detection and risk management: By continuously scanning components against vulnerability databases like the NVD, SCA helps organizations quickly identify and assess known security issues in third-party libraries.
- License compliance tracking: Many open-source libraries are subject to licenses with specific usage conditions. SCA tools detect license types and flag potential violations, helping companies avoid legal and compliance risks.
- Remediation guidance and automation: SCA tools often provide actionable remediation advice, such as upgrade paths or safer alternatives for vulnerable components. Some integrate directly into CI/CD pipelines to automate these fixes.
- Audit and regulatory requirements: For industries with strict compliance needs, SCA supports audit trails and reporting to meet regulations such as ISO 27001, SOC 2, or industry-specific standards.
- Supply chain security: With rising threats like dependency confusion and malicious packages, SCA contributes to securing the software supply chain by monitoring and validating third-party code sources.
Enterprise software composition analysis market trends
According to recent research, the software composition analysis market is growing rapidly as enterprises increase their use of open-source components. The global market is valued at USD 328 million and is projected to reach about USD 2,012 million by 2034. This represents a compound annual growth rate (CAGR) of 19.86%. Growth is driven by rising cybersecurity threats, stricter regulatory requirements, and broader adoption of open-source software in enterprise development.
Large enterprises represent the biggest share of the market. Organizations of this size accounted for 58% of total market share. These companies manage complex IT environments and large volumes of third-party components, which increases their exposure to vulnerabilities and compliance risks. As a result, they invest in advanced SCA solutions that provide real-time scanning, compliance checks, and reporting capabilities.
Industry verticals such as banking, financial services, and insurance (BFSI) led the market with a 27% share, driven by strict compliance requirements and the need to secure digital banking platforms. Healthcare is expected to grow at the fastest rate due to increasing use of electronic health systems and regulatory requirements such as HIPAA.
Artificial intelligence is also shaping the enterprise SCA market. AI-based capabilities allow faster scanning of large codebases and earlier detection of emerging risks. This improves development efficiency and strengthens overall security posture, making SCA tools more effective in large-scale enterprise environments.
Key functions of enterprise SCA
Inventory and bill of materials (SBOM)
An essential capability of enterprise SCA is generating a detailed inventory of all open-source software, libraries, and dependencies within a codebase. This inventory, often called a software bill of materials (SBOM), documents every third-party component and its corresponding version used in an application. The SBOM provides an authoritative source for understanding what is included in software artifacts, which is crucial for audits, compliance, and supply chain transparency.
Organizations benefit from having accurate and up-to-date SBOMs, as regulatory standards increasingly require this level of documentation. SBOMs allow security and compliance teams to react quickly to new vulnerabilities or licensing changes, enabling targeted remediation without having to re-examine the entire codebase. The automation provided by SCA tools ensures SBOMs remain current as new components are added or updated in ongoing development.
Vulnerability management
SCA tools help enterprises identify and manage vulnerabilities within open-source dependencies by continuously scanning for issues listed in public vulnerability databases and proprietary feeds. When the scanner detects a vulnerable component, it flags the problem, provides contextual information, and often suggests remediation strategies such as updating to a patched version or applying mitigations. This proactive approach is critical for maintaining the security posture of modern applications.
Frequent vulnerability scans allow organizations to address risks early, ideally before deployment. SCA solutions also support ongoing risk monitoring as libraries and components evolve or as new security disclosures are published. This cycle of continuous scanning, alerting, and remediation is necessary for enterprises to keep their applications secure against dynamic threats in the open-source ecosystem.
License compliance
License compliance is another core function of SCA, as non-compliance with open-source licenses can expose enterprises to legal and financial repercussions. SCA tools automatically identify license types for all detected components, whether permissive (like MIT or Apache 2.0) or restrictive (like GPL). They highlight potential conflicts with organizational policies, third-party license requirements, or redistribution restrictions that may need to be addressed.
SCA helps organizations establish and enforce acceptable use policies by alerting on problematic licenses or components. Automating this process is important for ensuring compliance without slowing development. Well-configured SCA tools facilitate necessary due diligence, reduce legal risks, and help maintain trust with customers, partners, and regulators.
Risk assessment
Risk assessment in SCA focuses on determining the likelihood and impact of vulnerabilities or license violations within a software supply chain. Enterprise SCA tools score components based on their security, maturity, community support, and maintenance activity. This provides stakeholders with actionable insights on which dependencies warrant immediate attention versus those that pose minimal concern.
Risk assessment also considers transitive dependencies—packages brought in indirectly by top-level components—and helps teams prioritize fixes or replacements based on the actual risk to the application. By providing a risk-based lens on open-source usage, SCA supports smarter resource allocation and more effective risk mitigation strategies.
Developer integration
Integration with developer workflows is critical for the success of SCA programs. Leading tools embed scanning into integrated development environments (IDEs), source code repositories, and CI/CD pipelines. This enables developers to surface and address issues with open-source components early, often at the point of introduction or pull request, rather than after vulnerabilities reach production.
Integrated SCA empowers development teams to make informed component selections and resolve problems quickly, improving both security and productivity. Automation is key: findings and remediation suggestions are delivered contextually, reducing friction and making secure, compliant software the default outcome.
Related content: Read our guide to SCA security
Notable SCA tools for enterprise
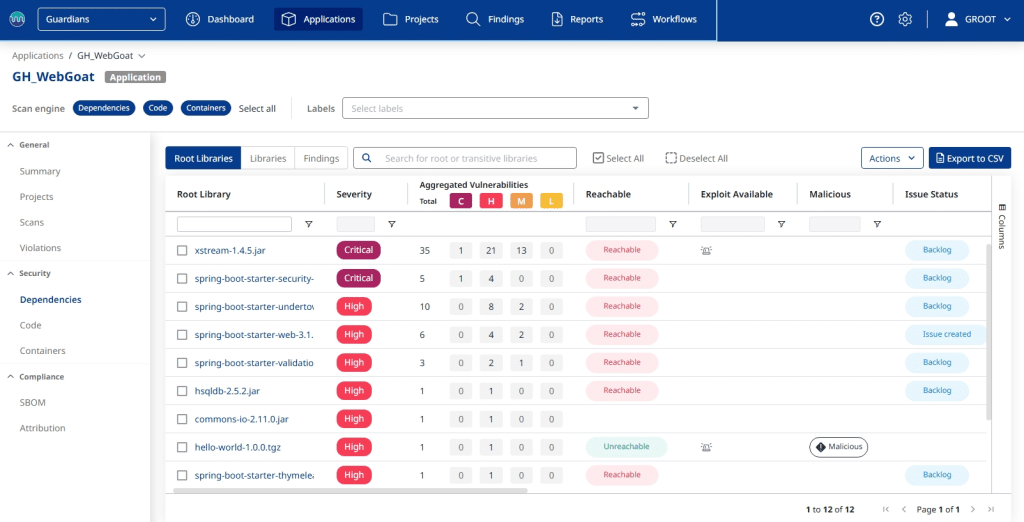
Mend.io
Mend SCA is an enterprise-grade software composition analysis solution and a core component of the Mend AI Native AppSec Platform. It is designed to manage and secure open-source dependencies at scale, going beyond basic scanning to prioritize reachable vulnerabilities specific to each application’s context and providing automated remediation to accelerate resolution. Mend SCA is part of a unified platform that also includes SAST, container security, AI security, and automated dependency updates under a single pricing model.
General features include:
- Reachability analysis: Determines whether vulnerable functions in direct and transitive dependencies are actually called by application code, reducing noise and focusing remediation on real risk
- Vulnerability scanning: Continuously scans open-source components against public databases and Mend’s proprietary vulnerability research, flagging known CVEs with severity ratings using CVSS 4.0
- License compliance management: Identifies open-source license types across all dependencies and flags conflicts with organizational policies to help avoid legal exposure
- CI/CD and repository integration: Embeds scanning into developer workflows across GitHub, Jenkins, Azure DevOps, Bamboo, and other CI systems without requiring developers to leave their environment
- Automated dependency updates: Works alongside Mend Renovate to automatically generate pull requests for dependency upgrades and vulnerability patches
Enterprise features include:
- SBOM generation and management: Produces and manages software bills of materials across the SDLC, supporting audit, supply chain transparency, and regulatory reporting requirements
- EPSS-informed prioritization: Combines CVSS 4.0 severity ratings with EPSS exploitability scores to help security teams focus on vulnerabilities most likely to be exploited in their specific environment
- Automated policy enforcement: Allows organizations to define custom security and license policies that automatically block builds or flag components that violate internal compliance standards
- AI component coverage: Analyzes dependencies introduced by AI-generated code and detects risks in embedded AI components including models, agents, and RAG pipelines
- Centralized reporting and dashboards: Provides unified visibility into vulnerability trends, license risk, and remediation progress across teams and repositories, supporting GRC and compliance workflows
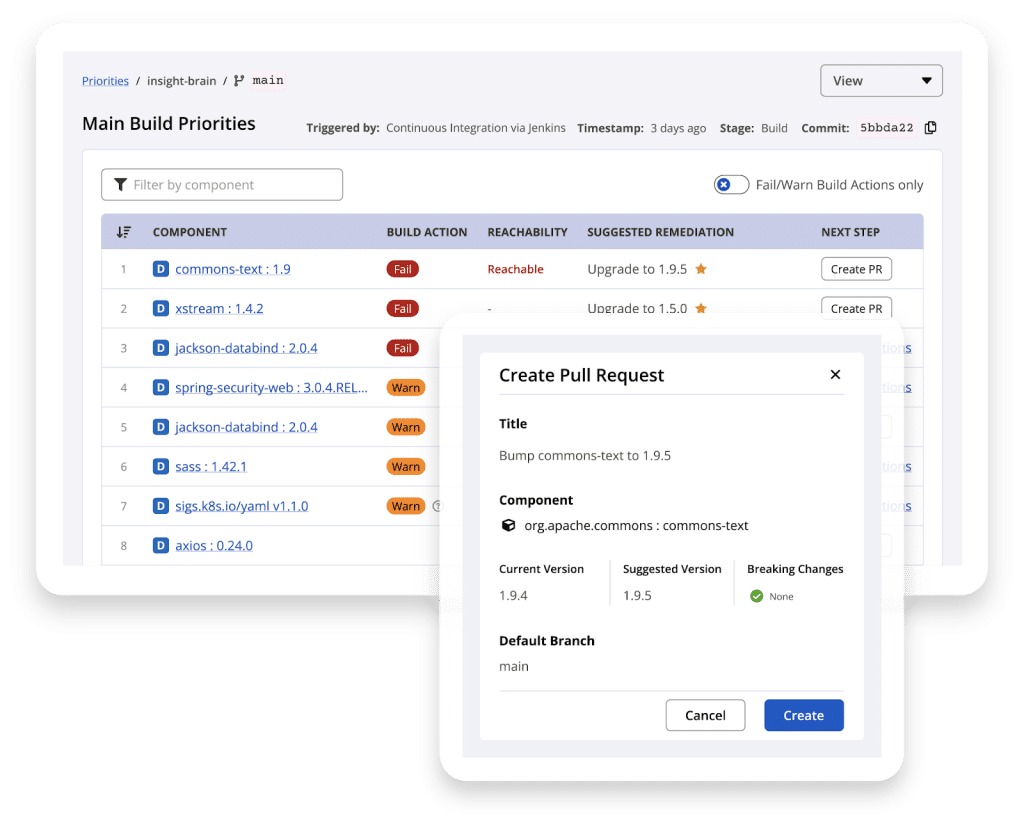
Snyk Open Source
Snyk Open Source is a developer-centric software composition analysis (SCA) tool to detect and remediate security vulnerabilities and license issues in open-source dependencies. It integrates directly into development environments and automation pipelines, allowing teams to find issues early, while coding, during pull requests, in CI/CD workflows, or even in production.
General features include:
- IDE and CLI integration: Detect vulnerable dependencies while coding, enabling developers to prevent security issues before they’re committed
- Pull request scanning: Test projects at the point of pull request to block vulnerable code from being merged
- CI/CD pipeline integration: Automatically enforce security checks during builds and deployments
- Production monitoring: Scan and monitor live environments to catch vulnerabilities that surface post-deployment
- Automated fixes: Generate pull requests with recommended upgrades or patches to resolve vulnerabilities quickly
Enterprise features include:
- Context-aware risk scoring: Combines vulnerability severity with business and application impact to prioritize threats that matter most
- Customizable remediation workflows: Supports one-click PRs with configurable templates to match internal development standards
- Continuous monitoring: Automatically watches for newly disclosed vulnerabilities, minimizing exposure time
- Security and compliance reporting: Provides historical and real-time reports tailored for security and governance teams
- Policy enforcement and governance: Tracks compliance with internal and external security requirements, supporting GRC efforts
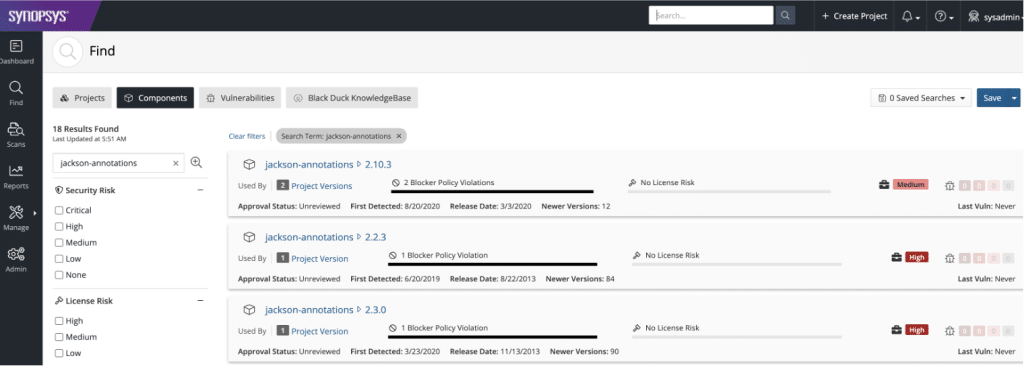
Synopsys Black Duck

Synopsys Black Duck is an enterprise-grade software composition analysis (SCA) solution to secure the software supply chain by identifying open-source components, vulnerabilities, and license risks across applications. It provides visibility into dependencies found in source code, containers, and binaries, including AI-generated code.
General features include:
- Dependency and binary scanning: Detects all open-source components in source code, containers, and compiled binaries
- IDE integration (Code Sight): Identifies vulnerable components within the IDE and offers remediation guidance at the point of development
- Flexible deployment: Available as a SaaS solution (Polaris fAST SCA), on-premises, or hosted, with support for air-gapped environments
- Automated governance: Enforces open-source policies through automated scanning and integration with DevOps pipelines
- Component health and license insight: Provides data on open-source license types, usage restrictions, and component maintenance status
Enterprise features include:
- SBOM generation: Produces detailed, accurate software bills of materials to support audit, compliance, and supply chain transparency
- BDSA-powered alerts: Delivers real-time vulnerability alerts and remediation advice via Black Duck Security Advisories, extending beyond NVD coverage
- Unified scanning infrastructure: Delivers consistent and scalable results across SaaS, on-premises, and IDE environments using a shared scanning engine
- Customizable policy management: Supports both prebuilt and custom governance rules to align with internal compliance standards and risk tolerance
- AI code coverage: Analyzes dependencies from AI-generated code for license and vulnerability risk
Checkmarx SCA

Checkmarx SCA is a core component of the Checkmarx One platform, to help organizations identify, prioritize, and remediate open-source risks—including vulnerabilities, malicious packages, and license violations. With an emphasis on detection accuracy and integration across the software development lifecycle, Checkmarx SCA offers security insights without disrupting developer workflows.
General features include:
- High detection accuracy: Industry-leading accuracy in identifying vulnerabilities, with zero false positives reported in third-party evaluations
- Transitive dependency scanning: Detects indirect dependencies to give full visibility into all open-source risks
- Malicious package detection: Identifies and flags intentionally harmful packages that could compromise software supply chains
- Exploitable path analysis: Determines whether a vulnerability is reachable or exploitable in the application context
- Remediation guidance: Provides actionable fix recommendations based on severity and exploitability
Enterprise features include:
- License risk management: Detects and classifies open-source licenses to ensure compliance with organizational policies
- Automated policy enforcement: Allows security teams to define custom rules and trigger automated actions for non-compliant components
- SBOM generation: Produces software bills of materials for regulatory compliance and supply chain transparency
- Correlated risk prioritization: Focuses remediation efforts on exploitable vulnerabilities to reduce noise and accelerate response
- Full SDLC coverage: Integrates SCA scanning throughout the entire development lifecycle, from code to deployment
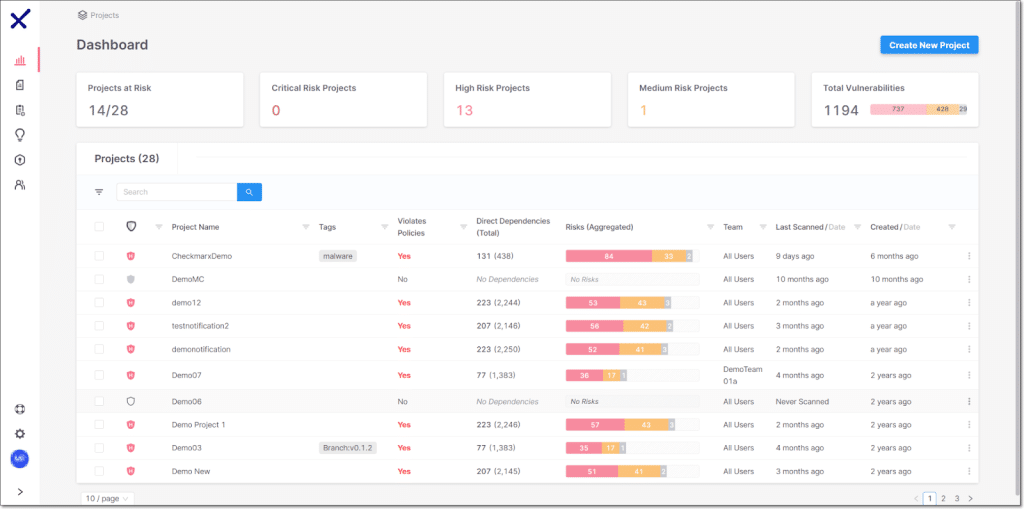
Source: Checkmarx
Veracode SCA

Veracode software composition analysis (SCA) enables development and security teams to detect, prioritize, and remediate open-source vulnerabilities and license risks. Built for modern development workflows, it integrates into developer environments and CI/CD pipelines, delivering fast scans and accurate results without slowing down release cycles.
General features include:
- Developer environment integration: Run scans and apply fixes directly from the IDE or CLI without leaving the development workflow
- Auto-remediation: Automatically generates context-aware pull requests to apply the best available fix
- Dependency graphs: Visualize and analyze direct and transitive dependencies to prioritize exploitable risks
- Proprietary vulnerability database: Detects known and emerging threats, including those not yet published in the NVD
- Fast setup and scanning: Start scanning in development environments within minutes with minimal configuration
Enterprise features include:
- Contextual risk prioritization: Prioritizes vulnerabilities based on exploitability and application impact, reducing noise and false positives
- Automated policy enforcement: Supports flexible governance with customizable policy rules and quality gates aligned to business needs
- Unified reporting and analytics: Consolidates security and license risk insights across teams, enabling cross-risk analysis and auditable mitigation
- Continuous code-to-cloud visibility: Maintains open-source security posture from development through deployment
- Expert support and guidance: Provides access to on-demand expertise for resolving complex open-source issues
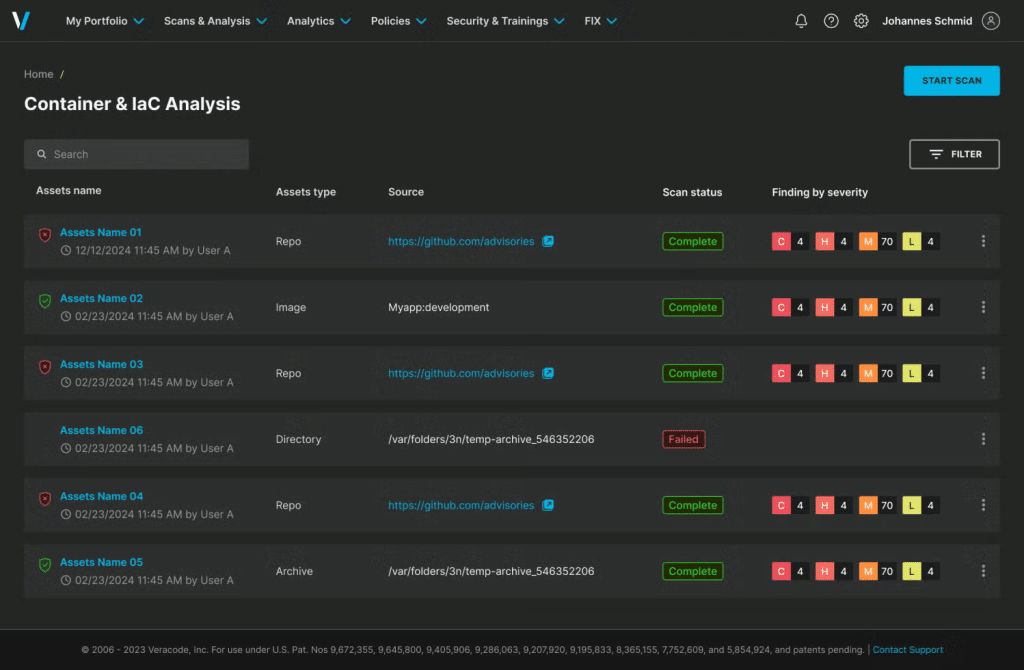
Source: Veracode
Sonatype Lifecycle

Sonatype Lifecycle is an enterprise SCA solution powered by Sonatype IQ Server. It identifies open-source risks and enforces custom security and license policies throughout the software development lifecycle. Lifecycle integrates with repositories, build systems, and developer tools to provide consistent governance from development through deployment.
General features include:
- Open-source risk identification: Detects vulnerable and policy-violating components across the SDLC
- Custom policy creation: Allows teams to define security and license rules aligned with internal standards
- SDLC-wide enforcement: Applies policies consistently during development, build, and release stages
- Integration ecosystem: Connects with repository managers, CI/CD tools, and developer environments
- Release and update tracking: Provides visibility into changes through documented release notes and versioning
Enterprise features include:
- Centralized IQ Server engine: Uses a unified scanning engine across Lifecycle and related Sonatype products
- Flexible deployment models: Available as self-hosted, cloud, or SaaS offerings
- Policy enforcement at scale: Enforces governance across large, distributed development teams
- Supply chain control integration: Works alongside repository firewall and SBOM management capabilities
- Enterprise support and documentation: Offers structured onboarding and ongoing platform guidance
Source: Sonatype
FOSSA

FOSSA is an enterprise platform for managing software supply chain risk, focusing on license compliance, vulnerability management, and SBOM automation. It scans dependencies across the SDLC and applies automated policy enforcement to prevent security and legal issues before release.
General features include:
- Comprehensive dependency scanning: Analyzes packages, containers, SBOMs, binaries, and code snippets
- License compliance management: Detects license types and helps prevent intellectual property violations
- Vulnerability management consolidation: Unifies security scanning across development stages
- Automated policy enforcement: Blocks or flags issues based on defined compliance rules
- SBOM generation and reporting: Produces SBOMs and license attribution reports for regulatory needs
Enterprise features include:
- Regulatory compliance support: Helps organizations meet SBOM and reporting requirements
- Obsolescence management: Tracks outdated and end-of-life dependencies
- Supplier risk management: Supports due diligence for third-party software components
- Broad ecosystem support: Covers major programming languages, frameworks, and CI/CD runtimes
- Enterprise onboarding and support: Includes structured implementation and support options
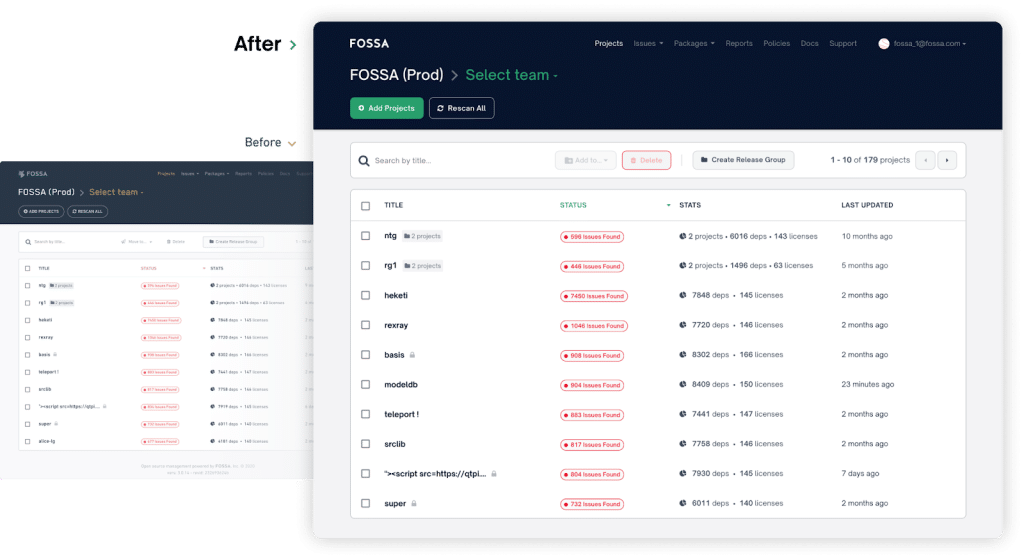
Source: FOSSA
OWASP Dependency-Track

OWASP Dependency-Track is an open-source platform for component analysis and SBOM-driven risk management. It ingests and produces CycloneDX SBOMs and tracks component risk across an organization’s software portfolio. The platform integrates with multiple vulnerability intelligence sources and supports risk prioritization and compliance workflows.
General features include:
- CycloneDX SBOM support: Consumes and produces CycloneDX SBOM and VEX documents
- Full-stack component tracking: Supports applications, libraries, containers, operating systems, firmware, and services
- Vulnerability intelligence integration: Aggregates data from sources such as NVD, GitHub Advisories, Sonatype OSS Index, and VulnDB
- Exploitability prioritization: Incorporates EPSS scoring to assist in mitigation prioritization
- Auditing workflow: Provides structured triage and review processes
Enterprise features include:
- Portfolio-wide component visibility: Tracks usage across all applications and identifies affected assets quickly
- Policy engine: Supports global and per-project policies for security, license, and operational risk
- Private vulnerability database: Maintains internal records of vulnerable components
- Enterprise integrations: Connects with security platforms such as Kenna Security, Fortify SSC, ThreadFix, and DefectDojo
- Authentication and access control: Supports OAuth 2.0, OpenID Connect, LDAP, Active Directory, and API keys
- API-first architecture: Provides OpenAPI-documented APIs for integration and automation
Source: OWASP
Conclusion
Software composition analysis has become a foundational element of modern application security, especially at the enterprise level where open-source usage is broad and complex. By automating the detection of vulnerabilities, managing license compliance, and enabling risk-based decision-making, SCA tools help organizations secure their software supply chains without slowing development. When integrated into developer workflows and governance frameworks, SCA provides continuous, scalable protection that aligns with both security objectives and business needs.