Mend Container
Secure containerized applications
Mend Container offers a full-stack container security scanning solution with image scanning, reachability analysis, code to cloud, secret scanning, K8s integration and Infrastructure as Code (IaC).










How Mend Container helps you secure containerized applications
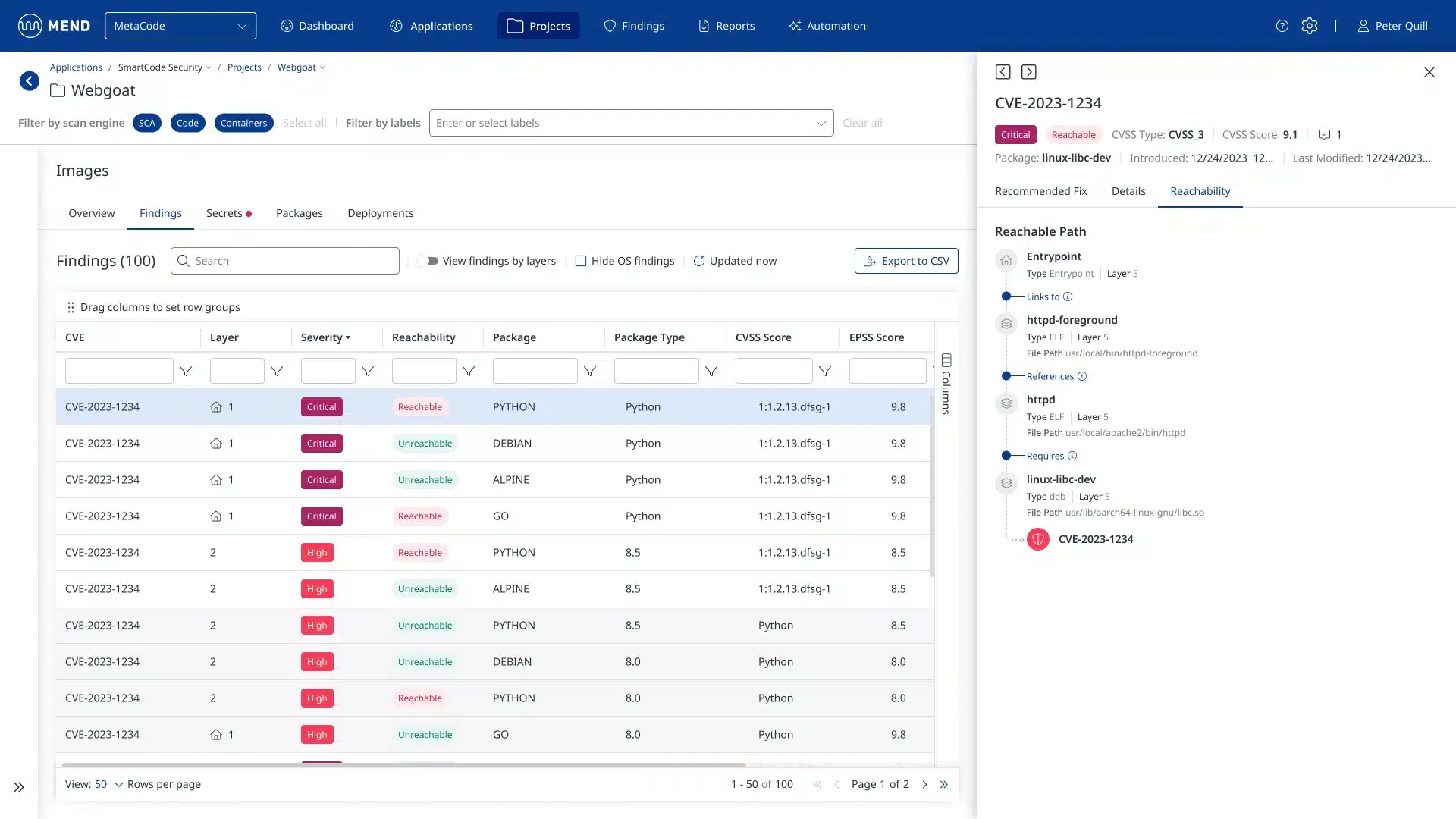
Container reachability analysis
Traditional vulnerability detection is just not enough to help your devs reduce risk efficiently.
Mend Container offers an innovative, agentless reachability analysis, identifying which vulnerable methods are actually being used at runtime, both on the application layer and the container layer.
Enable your teams to prioritize remediation efforts on vulnerabilities that pose an actual threat.
Development to deployment
Find vulnerabilities found in container images early in development, identify threats during runtime, and pinpoint the root location for rapid remediation.
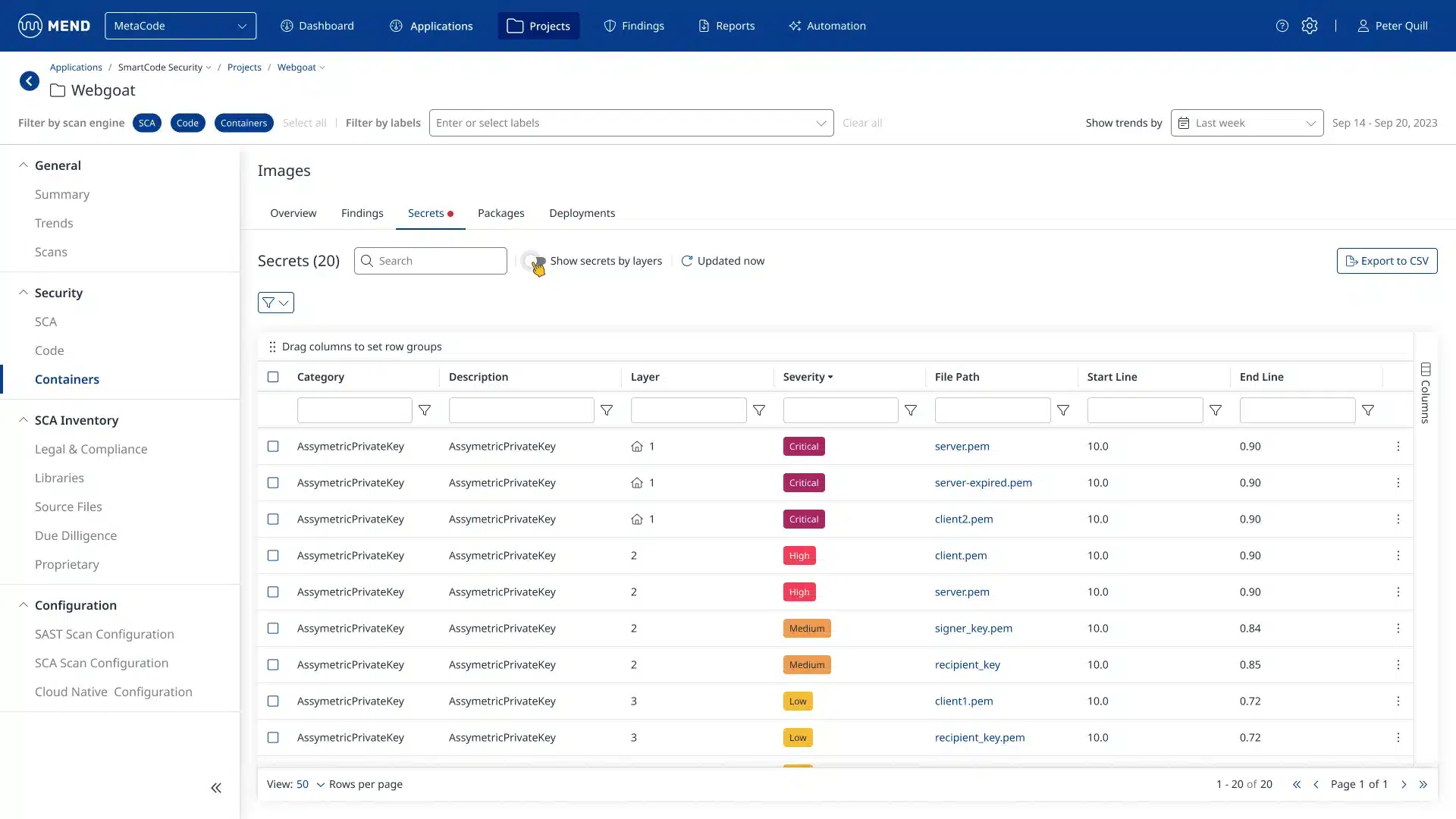
Secret scanning
Imagine a world where sensitive information like passwords, credentials, keys, and certificates never slip through the cracks in your container images.
Mend Container goes beyond surface layers, meticulously sifting through every nook and cranny, including filesystems and code repositories, to unearth hidden secrets that could expose your systems.
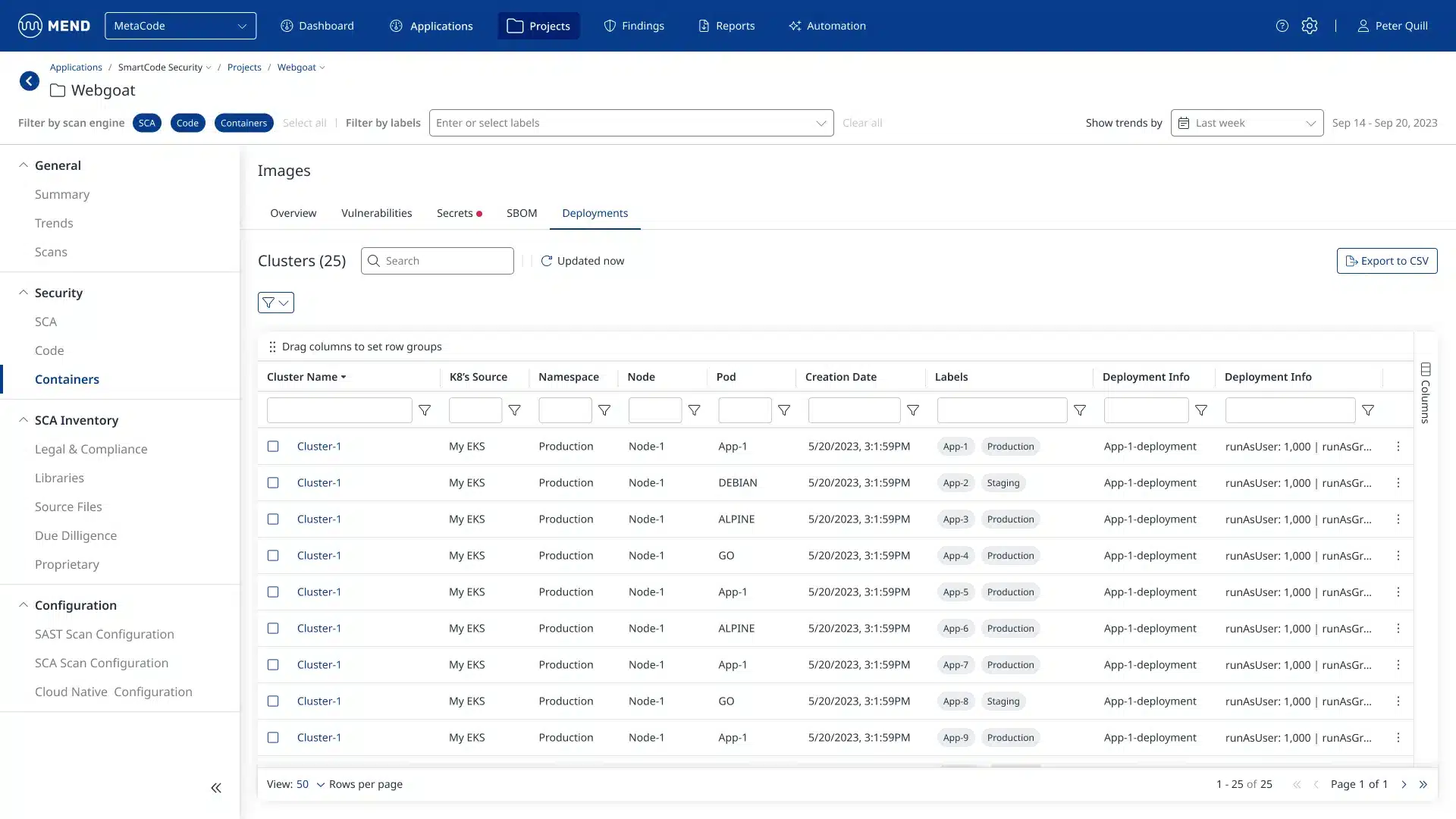
K8s cluster scanning
Streamline your security process by automatically scanning all running container images within your Kubernetes clusters.
This comprehensive view will allow your teams to identify and label deployed containers, ensuring you focus on securing the versions critical to your operations.
Explore Mend Container, part of the Mend AppSec Platform
Mend Container is a key component of the Mend AppSec Platform’s holistic and proactive approach to application security.
Stop playing defense against alerts.
Start building a proactive AppSec program.