
Bigger Data, Bigger Problems: Three Major Challenges in Big Data Security

New ESG Research Report Outlines Best Practices for Effective Application Security Programs
Cybersecurity Awareness Month 2023: Five Reasons You Need Automatic Software Updates for Your Application Security.
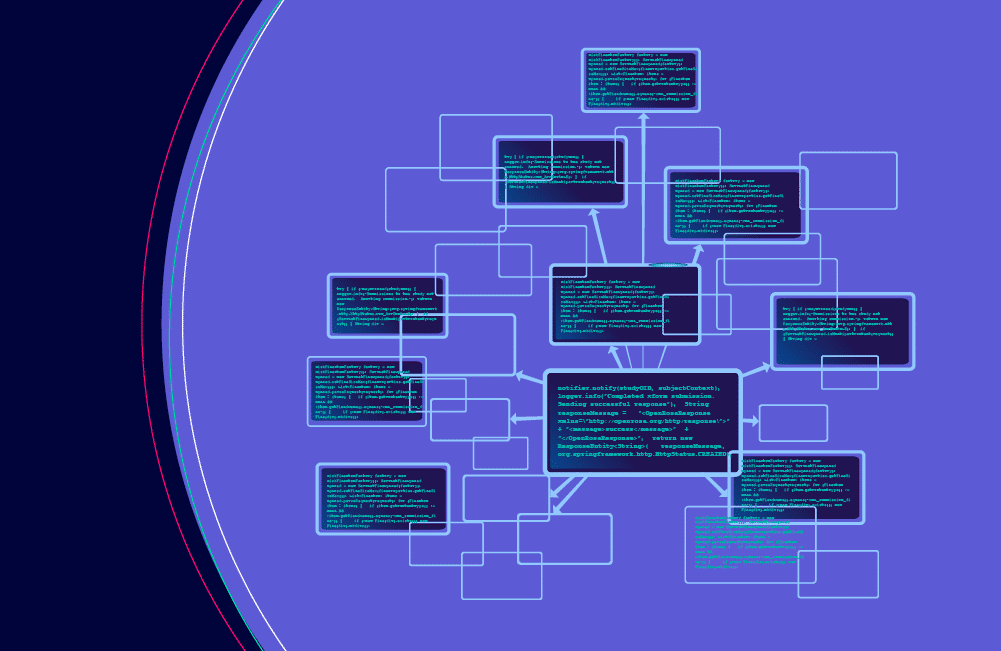
What Role Should Dependency Management Play as the Regulation of the Software Supply Chain Escalates?

Why is Software Vulnerability Patching Crucial for Your Software and Application Security?