Table of contents
From Panic to Playbook: Modernizing Zero‑Day Response in AppSec
Why the next Log4Shell will be won or lost in the first 72 hours—and what a modern zero‑day workflow looks like.
Every security team remembers where they were when Log4Shell dropped. A quiet Friday afternoon in December 2021 turned into a weekend of war rooms, emergency patches, and executive updates. Years on, the Log4j fallout still shows up in breach reports—a stubborn reminder that zero‑days don’t end when the news cycle does.
Zero‑day events aren’t rare anymore. They’re a recurring operational reality, and the gap between disclosure and exploitation keeps narrowing. Attackers routinely weaponize newly disclosed CVEs within hours. That means the first 24–72 hours after disclosure—the window when most organizations are still trying to figure out whether they’re affected—is exactly the window adversaries are trying to exploit.
The question for AppSec leaders isn’t whether the next zero‑day is coming. It’s whether their team will respond in hours or in days.
Why zero‑days break traditional AppSec workflows
A normal vulnerability lifecycle moves at a predictable pace. A CVE is published, a detection rule is added to a scanner, the next scheduled scan surfaces it, a ticket is filed, and a fix lands in the next sprint. That cadence works for the vast majority of vulnerabilities that don’t demand drop‑everything urgency.
Zero‑days break that model in three ways.
Speed. Time‑to‑disclosure and time‑to‑exploit have collapsed. Waiting for the next scheduled scan isn’t an option.
Data volatility. The intelligence itself is messy in the early hours. Affected versions get revised, indicators of compromise evolve, and “patched” libraries sometimes turn out to still be vulnerable. Any response that relies on static spreadsheets, email threads, or one‑off PDFs goes stale the moment it’s sent.
Blast radius. “Where am I exposed?” is deceptively hard. A single vulnerable library can be buried three layers deep in a transitive dependency or sitting inside a container image that hasn’t been rebuilt in six months. Answering “am I affected?” at 2 a.m. requires correlating live threat intelligence against a current, trustworthy inventory of everything you’ve ever shipped.
What modern zero‑day management looks like
Teams that respond well to zero‑days share a few characteristics. They don’t treat a zero‑day as a new project—they treat it as a known workflow that gets activated on demand. That workflow usually has four pieces:
- A live, authoritative source of zero‑day data decoupled from scan schedules.
- Automatic correlation that maps the zero‑day against existing inventory without requiring a fresh scan.
- A clear lifecycle for each event—when it’s active, when it’s no longer an immediate threat, when it moves to the history books.
- A shared audit trail so security, engineering, and compliance all speak from the same source of truth.
That’s the model we’ve built into the Mend AppSec Platform. Here’s how each piece works in practice.
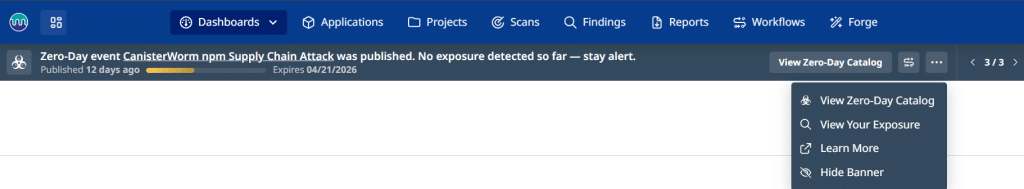
Zero‑day data as a live feed, not a spreadsheet
The Mend platform includes a dedicated Zero‑Day Data page—a live, UI‑based and API‑backed view of every zero‑day Mend.io is actively tracking. It’s accessible directly from the user profile menu, and importantly, it’s independent of your inventory. You can see what Mend.io is tracking before, during, and beyond your own scans. That matters, because the first question during a zero‑day is usually “what do we actually know?”—and the answer needs to come from a single, authoritative feed, not a patchwork of vendor advisories.
The page defaults to the most recent active zero‑day and lets you switch between Active events and Historical ones, which remain available indefinitely. For each entry you can see the library name, SHA‑1, vulnerability ID, date added, and zero‑day name—and export the whole view to CSV or JSON for internal reporting or audit purposes. The static spreadsheets that used to circulate during a Log4Shell‑style event are replaced with a live data source that both humans and tooling can consume.
Correlating the event against your inventory
Knowing what’s out there is only half the job. The harder question—where am I exposed?—is answered with a single click. The View Full Exposure button on the Zero‑Day Data page navigates directly to a zero‑day findings report scoped to your organization’s inventory.
The correlation logic uses your existing scan data as the source of truth, matching on either MSC ID or library name. Critically, no new scan is automatically triggered—Mend.io uses what you’ve already scanned to determine impact. That design choice is deliberate. During a zero‑day, you don’t want to wait for a full re‑scan of a monorepo; you want an immediate answer based on what you already know, with the option to run follow‑up scans on the components that matter.
A defined lifecycle for every event
Zero‑days also have a time dimension most tooling ignores. In the Mend platform, each event progresses through two phases.
Active phase (Days 0–30). Awareness and violation banners appear where relevant, the Zero‑Day Data page marks the event as Active, and inventory correlation runs against existing scans.
Expired phase (after Day 30). Banners come down, the status flips to Expired, and the event shifts from incident‑response mode to historical record. The data remains available indefinitely for audits and retrospectives.
That 30‑day window maps to how zero‑days actually behave in the wild. The first month is when attention, patching, and executive interest peak. After that, the vulnerability either gets absorbed into routine vulnerability management or becomes a historical reference point. Building that lifecycle into the tool itself means your team doesn’t have to guess when to stop paying close attention.
From reactive to prepared
None of this eliminates the stress of a zero‑day—nothing will. But it changes the nature of the work. Instead of spinning up a new process every time a CVE makes the news, your team follows a known playbook: check the live feed, run the exposure report, track the event through its lifecycle, and share a consistent, exportable view with stakeholders.
The next Log4Shell is coming. The organizations that weather it well won’t be the ones with the biggest security budgets. They’ll be the ones whose zero‑day response is already a rehearsed workflow—not an improvisation.
See it in action
Explore zero‑day management in the Mend AppSec Platform—read the documentation or schedule a demo to see how your team can move from panic to playbook.





