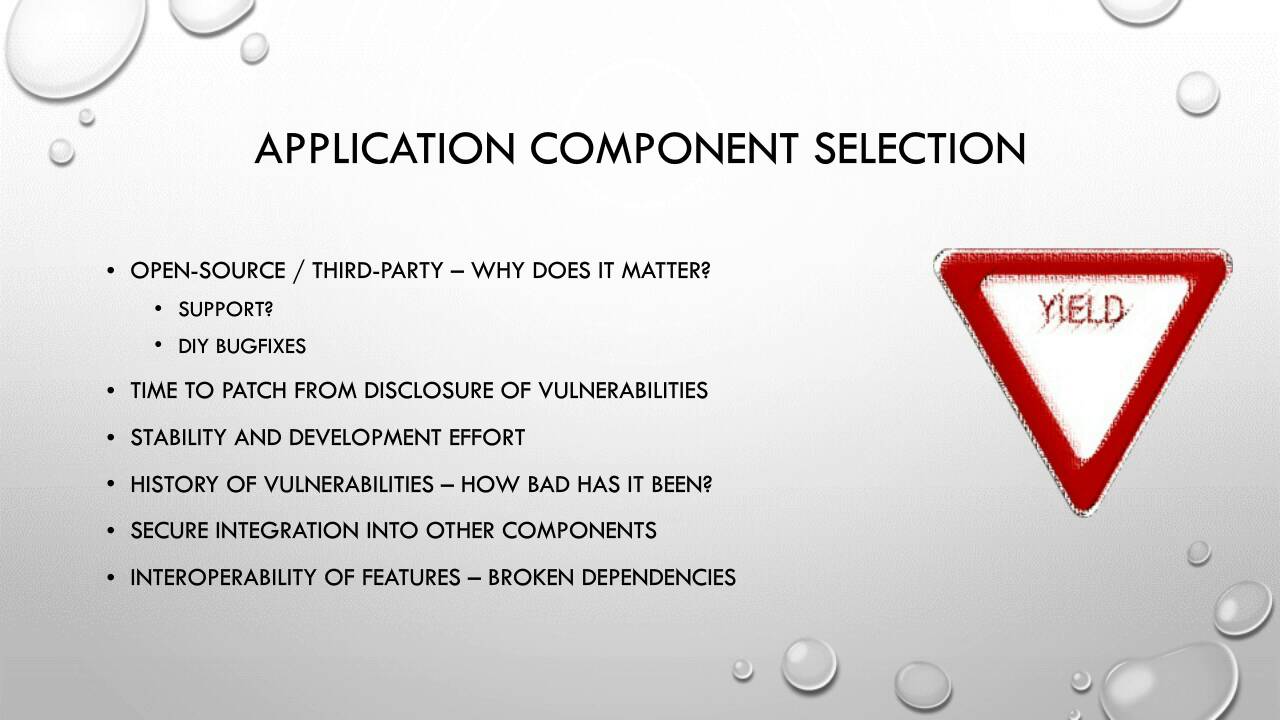
Advance From Open Source Code Scanner to Software Composition Analysis Solution
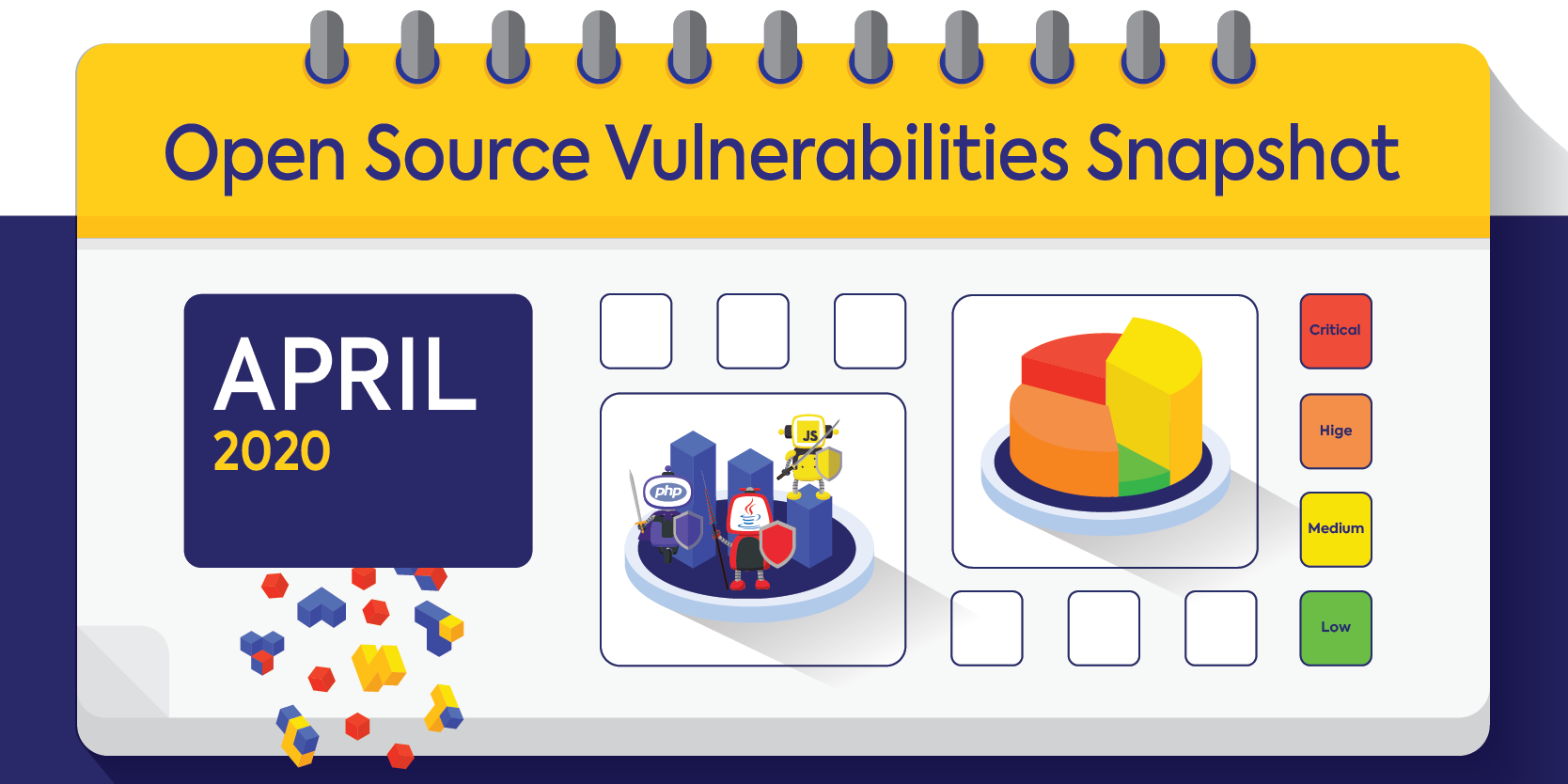
Discover why it's essential to advance from open source code scanners to software composition analysis solutions. Learn about the pitfalls of outdated scanners and the benefits of modern tools.