Table of contents
Best Application Security Testing Solutions: Top 12 in 2026

What are application security testing solutions?
Application Security Testing (AST) solutions use methods like SAST, DAST, IAST, and SCA to find vulnerabilities in software. They integrate into the SDLC to scan code (SAST), test running apps (DAST), monitor live execution (IAST), and check dependencies (SCA) for flaws, protecting against threats like SQLi, XSS, and insecure components. Top tools include Mend.io, SonarQube, and Checkmarx.
Main types of AST solutions:
- SAST (Static AST): Analyzes source code, bytecode, or binaries without running the app to find insecure patterns early.
- DAST (Dynamic AST): Tests live, running applications from the outside, simulating attacks like XSS and SQL Injection.
- IAST (Interactive AST): Combines SAST & DAST by using agents inside the application during testing for real-time monitoring, reducing false positives.
- SCA (Software Composition Analysis): Scans open-source and third-party libraries for known vulnerabilities and license issues.
Application security testing market trends
According to recent market research, the Application Security Testing (AST) market is demonstrating robust and sustained growth, driven by escalating cyber threats, rapid digital transformation, and increasing DevSecOps adoption across enterprises.
The global AST tools market is valued at approximately USD 5.2 billion and is forecast to more than double to around USD 13.7 billion by 2033, representing a compound annual growth rate (CAGR) of about 11.5%.
A key factor behind this growth is the adoption of “shift-left” security practices that integrate AST earlier in the software development life cycle. DevSecOps teams are increasingly embedding testing tools into CI/CD pipelines so that vulnerabilities are detected during coding and build stages rather than after deployment. Over 78% of organizations reported integrating security testing before production.
Cloud-native architectures and API-centric applications are also fuelling demand for AST capabilities. As more enterprises move workloads to microservices and distributed platforms, AST solutions that support container environments and real-time application monitoring are expanding in importance. Additionally, the Software Composition Analysis (SCA) segment, focused on scanning third-party libraries for known vulnerabilities, continues to gain traction as organizations grapple with the risks posed by open-source dependencies.
Core categories of application security testing solutions
Static application security testing (SAST)
Static application security testing (SAST) examines source code, bytecode, or binaries for security vulnerabilities without executing the program. It allows developers and security professionals to analyze code systematically and identify flaws such as buffer overflows, injection threats, and insecure coding patterns early in the software development lifecycle. The early detection capability makes SAST valuable by enabling developers to remediate vulnerabilities before applications move to later stages of development, where fixes are costlier and riskier to implement.
SAST tools integrate well with popular integrated development environments (IDEs) and continuous integration pipelines, providing actionable feedback within a developer’s normal workflow. This integration helps maintain software quality and security standards continuously as new code is written and merged. Limitations of SAST include potential false positives and challenges in analyzing complex, dynamically created code, but its benefits for early-stage vulnerability detection make it a cornerstone of secure software development practices.
Dynamic application security testing (DAST)
Dynamic application security testing (DAST) evaluates running applications to identify vulnerabilities in their operational environment. Unlike SAST, which inspects static code, DAST interacts with deployed applications in real-time, simulating attacks and monitoring application responses for signs of security weaknesses, such as improper input validation, authentication issues, or session management flaws. This approach is particularly effective in discovering vulnerabilities that only manifest when the application is live and processing requests.
DAST tools are black-box testers—they do not require access to source code and assess applications much like an external attacker would. These tools are essential for security assurance in web applications and APIs where runtime behaviors, third-party integrations, and misconfigurations can introduce risks. However, DAST can struggle with full coverage, especially for applications requiring authentication or those that are heavily client-side, but it remains a critical layer in security testing strategies.
Interactive application security testing (IAST)
Interactive application security testing (IAST) combines aspects of both SAST and DAST, analyzing applications dynamically while they are running, but with more context and detail. IAST solutions instrument the application or its runtime environment, monitoring code execution, data flow, and application behavior as actual test cases or real users interact with the application. This context-rich approach allows IAST tools to deliver accurate and actionable vulnerability insights with fewer false positives compared to traditional SAST or DAST.
IAST tools function best within modern DevOps pipelines, providing continual feedback as code changes and new builds are deployed. Because IAST observes the application from the inside, it can directly correlate detected vulnerabilities to specific lines of code, frameworks, or libraries. This direct mapping expedites remediation efforts for development teams. However, IAST may introduce minor performance overhead and requires integration with the application at runtime, leading to consideration for appropriateness in specific production environments.
Software composition analysis (SCA)
Software composition analysis (sca) focuses on identifying risks associated with open-source and third-party components used in an application. Modern software development frequently relies on these ready-made libraries to accelerate delivery, but these components can introduce well-known vulnerabilities and licensing issues if not properly managed. sca solutions scan the application’s dependencies, cross-referencing them with public vulnerability databases and licensing repositories to flag at-risk packages.
Effective sca tools provide continuous monitoring for new vulnerabilities discovered after components are integrated, ensuring organizations remain protected as security advisories are published. They deliver actionable intelligence regarding which dependencies pose the greatest risk and where urgent updates or patches are required. sca is essential for regulatory compliance and managing supply chain risks, but it should be complemented by SAST, DAST, and IAST for comprehensive security coverage.
Related content: Read our guide to application security testing tools
Notable application security testing solutions
SAST
Mend SAST
Mend SAST is a static application security testing solution built for enterprise development teams that need to secure both human-written and AI-generated code without slowing down delivery. Its on-premises scanning keeps sensitive data private while generating compliance reports, enforcing quality gates and SLAs, and streamlining workflow automations in the cloud. Its enhanced engine identifies vulnerabilities in source code with high precision and recall, helping teams remediate real risks earlier in the SDLC.
Key features include:
- Gen-2 scanning engine: Delivers 38% better precision and 48% better recall than competitors, cutting through noise to surface what truly matters, where developers code
- AI-powered remediation: Feeds vulnerability information into AI code assistants to automatically remediate custom code flaws directly in the AI workflow, with fixes that are 46% more accurate than competitors
- Incremental scanning: Pinpoints new vulnerabilities linked to recent code changes directly within the repository, grouping related findings to reduce alert fatigue
- Broad language and toolchain support: Integrates with IDEs, repositories, pipelines, and other dev tools, supporting more than a dozen programming languages
- Unified AppSec platform: Scan results appear alongside Mend AI, Mend SCA, Mend Renovate, and Mend Container, all in one platform
SonarQube

SonarQube’s SAST solution provides static analysis capabilities that go beyond first-party code to uncover vulnerabilities in third-party libraries. Its taint analysis tracks the flow of untrusted data through the application stack, including interactions with external dependencies, making it possible to detect injection flaws and hidden security risks that traditional SAST tools often miss.
Key features include:
- Cross-boundary taint analysis: Traces data flow across both first-party and third-party code to uncover deeply hidden vulnerabilities
- Wide language support: Covers 35+ programming languages including Java, C#, Python, JavaScript, and more
- Compliance alignment: Security rules mapped to standards such as OWASP Top 10, CWE Top 25, PCI DSS, and STIG
- Security hotspots: Flags sensitive code requiring human review, enhancing developer awareness and secure coding practices
- Automated fix guidance: Provides actionable remediation steps with contextual code highlights and AI-powered fix suggestions
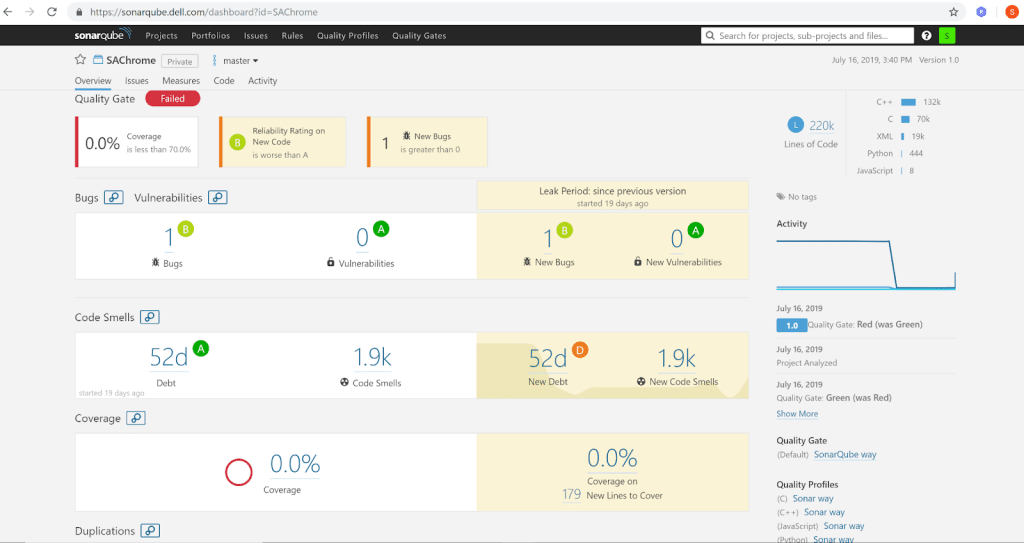
Source: SonarSource
Checkmarx

Checkmarx SAST delivers a static analysis engine designed to balance speed and accuracy. Its solution is built for enterprise-scale applications, helping development teams detect security flaws early without compromising productivity. With capabilities like adaptive scanning, customizable queries, and uncompiled code analysis, Checkmarx enables teams to reduce false positives and fix vulnerabilities faster.
Key features include:
- Adaptive vulnerability scanning: Dynamically adjusts scan depth to prioritize relevant vulnerabilities and protect critical applications
- Best fix location guidance: Pinpoints the most effective place in the code to apply a fix, reducing remediation time
- AI query builder: Automates the creation of security queries tailored to your codebase, enhancing detection precision
- AI security champion: Uses AI to assist developers with security best practices during development and triage
- Uncompiled code scanning: Detects vulnerabilities in raw code before build stages, enabling earlier remediation
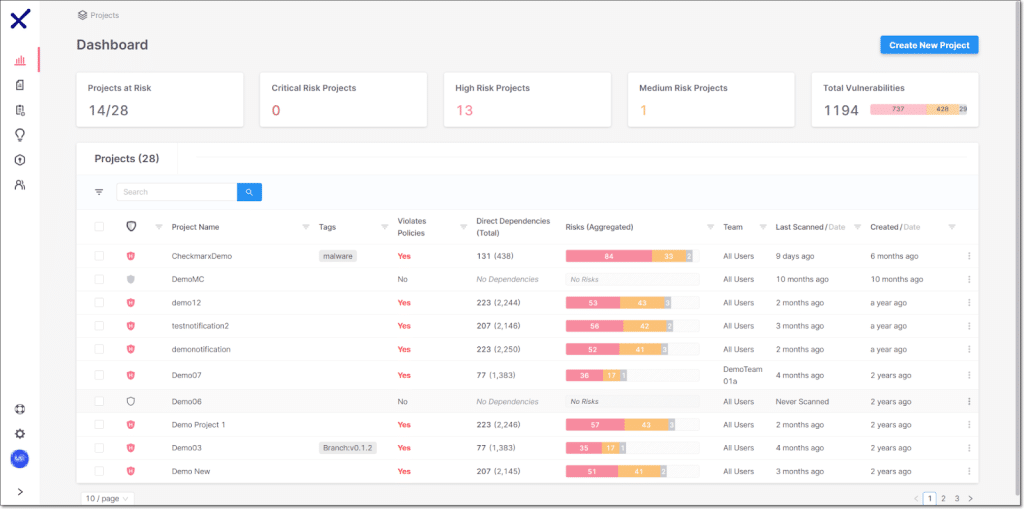
Source: Checkmarx
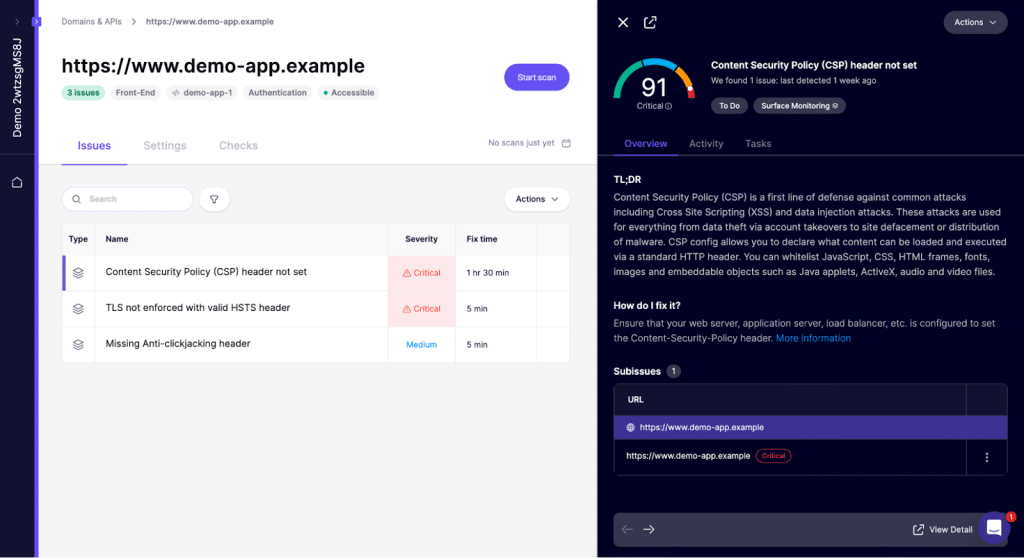
DAST
Burp Suite
Burp Suite’s DAST solution automates dynamic application security testing at scale, allowing organizations to secure web applications and APIs throughout the software development lifecycle. Built on the trusted Burp technology used by security professionals worldwide, it enables continuous scanning without overwhelming AppSec teams.
Key features include:
- Scalable dynamic scanning: Automates DAST across large web portfolios, enabling recurring scans on thousands of sites with simple URL-based setup
- Accurate detection with fewer false positives: Built on the proven Burp Scanner engine, delivering reliable findings with minimal alert fatigue
- Strong API and authentication support: Effectively tests modern web apps and APIs, including complex authentication flows
- Seamless CI/CD integration: Integrates with tools like Jira, GitLab, Trello, and any CI/CD pipeline via a GraphQL API
- Real-time dashboards and reporting: Visualize security posture trends and generate reports tailored to compliance needs
Zed Attack Proxy (ZAP)
ZAP (Zed Attack Proxy) is a free and open-source DAST solution designed to detect vulnerabilities in web applications through active scanning. Its GitHub Action integration allows users to automate full scans directly in their CI workflows, where ZAP actively crawls and attacks a target application to uncover security issues.
Key features include:
- Active dynamic scanning: Performs full attack simulations to uncover vulnerabilities not detectable via passive scans
- GitHub Action integration: Automates scans within CI pipelines by running as part of GitHub Actions
- Continuous issue tracking: Creates and updates GitHub issues based on scan results, alerting developers to new or resolved vulnerabilities
- Flexible targeting: Can scan both publicly accessible and local development environments
- Spider and AJAX crawling: Uses both standard spidering and AJAX-based techniques to maximize application coverage
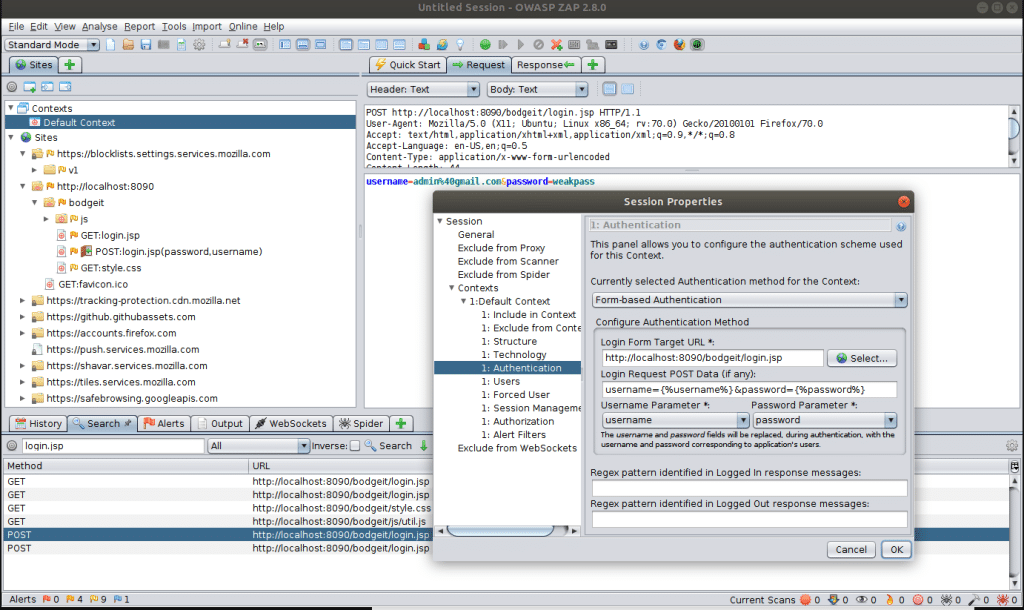
Source: Zaproxy
Acunetix

Acunetix delivers a dynamic application security testing (DAST) solution that automates web application and API scanning across the full lifecycle of AppSec. Designed for fast, accurate vulnerability detection, it combines deep crawling, machine learning-based risk assessment, and blended DAST + IAST scanning.
Key features include:
- Comprehensive discovery and crawling: Automatically maps all web assets, including SPAs, unlinked files, and API endpoints often missed by other scanners
- Deep application coverage: Crawls and scans JavaScript-heavy apps and password-protected areas using macros
- Predictive risk scoring: Uses AI/ML models to assess and prioritize risk before scans begin, improving focus and efficiency
- Wide vulnerability detection: Detects over 12,000 known vulnerabilities, including zero-days, using fast, accurate scanning
- Blended DAST + IAST scanning: Enhances detection by combining external attack simulation with internal application behavior monitoring
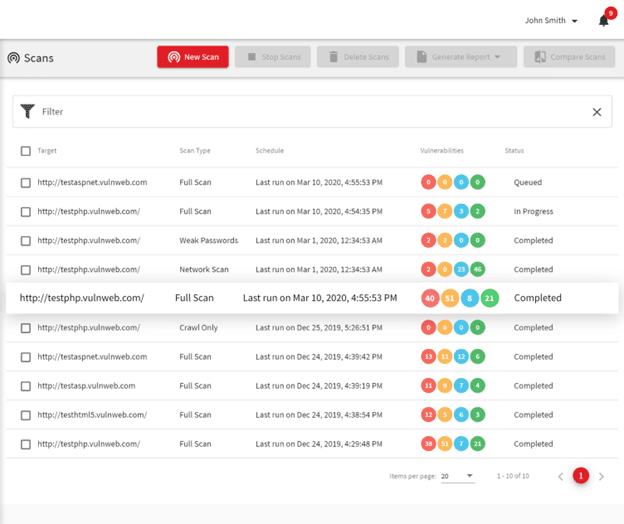
Source: Acunetix
IAST
HCL AppScan

HCL AppScan offers an interactive application security testing (IAST) solution that provides real-time vulnerability detection by observing applications during runtime. It integrates seamlessly into the software development lifecycle (SDLC), operating during functional tests or QA to deliver detailed, context-aware insights into both source code and live behavior.
Key features include:
- Runtime code monitoring: Captures live interactions within applications and APIs to detect vulnerabilities with contextual accuracy
- Auto-issue correlation: Automatically groups related findings across SAST, DAST, and IAST to streamline remediation and reduce noise
- API discovery and risk insights: Automatically identifies internal APIs and enhances findings with software composition analysis (sca) data
- Patented Java deployment: Deploys as a Java agent or web app with minimal configuration, enabling faster startup and in-place upgrades without restarts
- Patented .NET integration: Operates directly in managed code within the .NET runtime, preserving performance while expanding detection depth
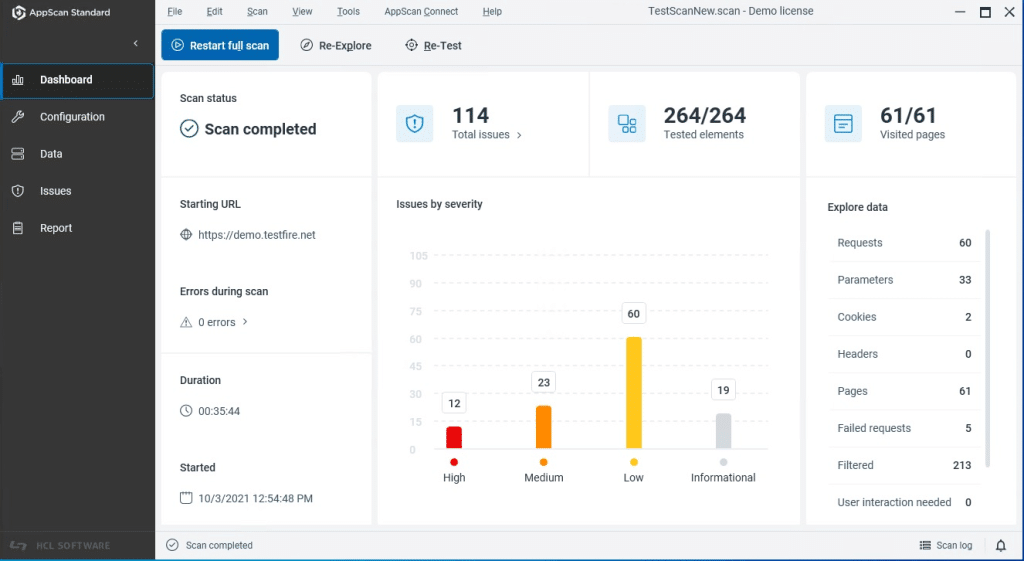
Source: HCL AppScan
Invicti

Invicti combines dynamic application security testing (DAST) with interactive application security testing (IAST) to deliver broad, accurate, and actionable vulnerability detection across web applications and APIs. The DAST engine identifies security flaws through external testing, while the Invicti Shark IAST sensor monitors the application from the inside, enabling deeper analysis.
Key features include:
- Combined DAST + IAST scanning: Integrates external and internal analysis to detect more vulnerabilities than either method alone
- IAST-driven coverage expansion: The sensor exposes hidden files, routes, and APIs, improving test depth and accuracy
- Proof-based scanning™: Verifies exploitable vulnerabilities automatically, reducing false positives and manual validation
- Precise remediation guidance: Pinpoints vulnerability locations down to file names and line numbers, with exploit evidence and stack traces
- Advanced API security testing: Supports REST, SOAP, and GraphQL APIs, including stateful, multi-step workflows and chained requests
Aikido

Aikido provides interactive and dynamic application security testing (IAST + DAST) as part of its unified, code-to-cloud security platform. Designed for modern, cloud-native development, Aikido’s solution monitors both runtime environments and application behavior to detect vulnerabilities such as SQL injection, XSS, and CSRF.
Key features include:
- Runtime-driven vulnerability detection: Simulates real-world attacks and monitors live applications for security flaws at runtime
- Authenticated DAST scanning: Tests secured areas of web apps and APIs to uncover deep-seated issues like injection and cross-site scripting
- Full API coverage: Scans every API endpoint for common vulnerabilities, using a Nuclei-based engine tailored to modern architectures
- CI/CD integration: Seamlessly plugs into development pipelines to catch issues before they reach production
- Low false positives: Uses triaging and reachability analysis to surface only meaningful, exploitable vulnerabilities
Source: Aikido DAST
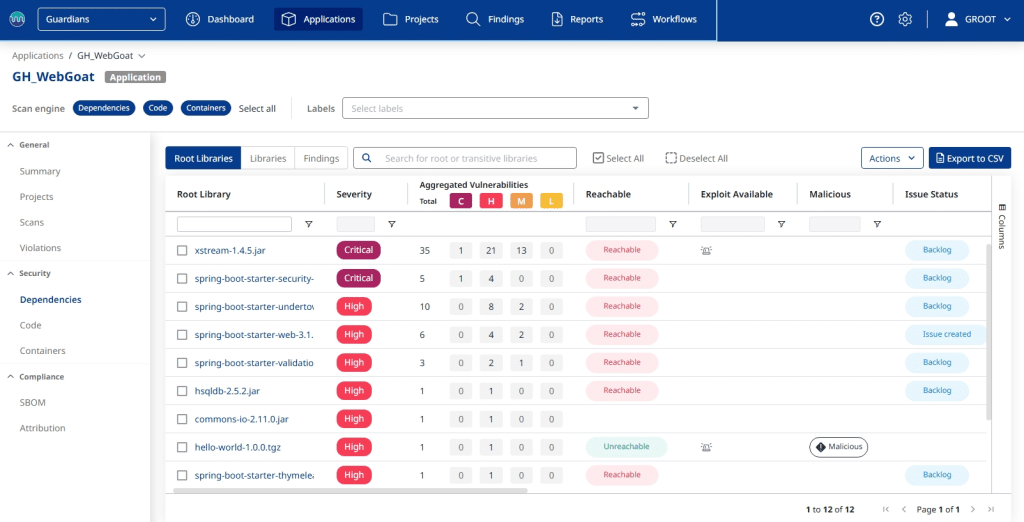
SCA
Mend SCA

Mend SCA is an enterprise-grade software composition analysis solution designed to manage the security and license risks of open-source dependencies throughout the software development lifecycle. It combines real-time, comprehensive discovery, reachability-based vulnerability prioritization, automated license compliance, and integrated dependency updates via Mend Renovate.
Key features include:
- Reachability-based prioritization: Employs unique reachability analysis to show whether application code actually interacts with vulnerable functions in both direct and transitive dependencies, including those that may pose a threat to AI models
- CVSS 4.0 and EPSS scoring: Utilizes CVSS 4.0 severity ratings to gauge potential vulnerability impact and incorporates EPSS exploitability data to assess the likelihood each vulnerability will be exploited
- Automated dependency updates: Mend Renovate detects newer package versions and creates pull requests directly in the repository, including detailed information about updates such as age, adoption, passing rates, and complete change logs
- License compliance enforcement: Issues real-time alerts when detected license types violate company policy, with automatic remediation capabilities and the ability to block license violations before they enter the codebase
- SBOM generation and CI/CD integration: Generates SBOMs, license reports, and compliance audit logs across large codebases and multiple repositories, integrating with Jenkins, Azure DevOps, Bamboo, GitHub, and other CI tools
Black Duck SCA

Black Duck by Synopsys provides a software composition analysis (sca) solution that helps organizations manage the risks of using open source and third-party code. By identifying vulnerabilities, license issues, and quality concerns in software dependencies, Black Duck gives teams full visibility into their software supply chain.
Key features include:
- Comprehensive dependency detection: Uses dependency, binary, codeprint, and snippet analysis to identify both declared and hidden components
- Security advisory integration: Leverages Black Duck Security Advisories to provide detailed vulnerability data and risk context
- License and quality risk management: Flags license compliance issues and component quality concerns alongside security findings
- SDLC integration: Embeds into development workflows and CI/CD pipelines to enforce policies and scan automatically at every stage
- SBOM generation and management: Supports SPDX and CycloneDX formats and automates SBOM creation and updates across the SDLC
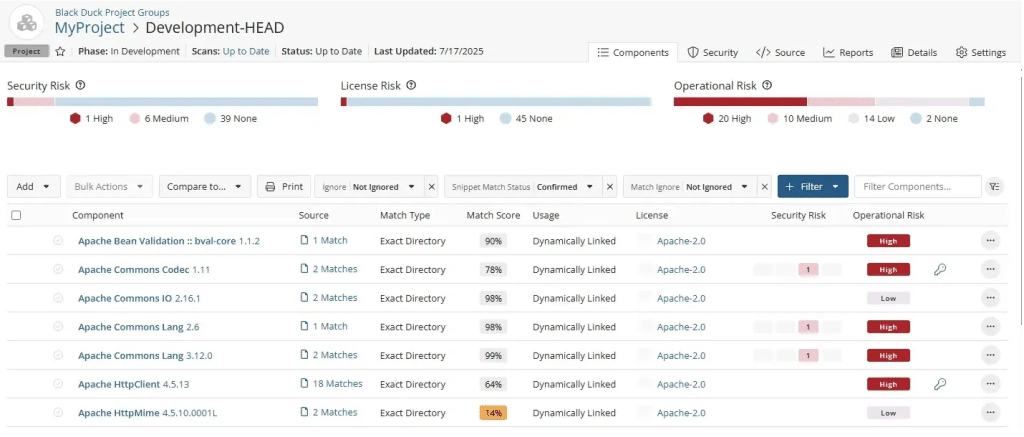
Source: BlackDuck
Snyk Open Source

Snyk Open Source offers a developer-first software composition analysis (sca) solution designed to identify and fix security and license issues in open source dependencies. Integrated into the tools developers already use (IDEs, CLI, SCMs, and CI/CD pipelines) Snyk makes it easy to detect vulnerabilities early and remediate them efficiently.
Key features include:
- Developer-centric integration: Embedded into IDEs, command line, Git repos, and CI/CD tools for real-time vulnerability detection
- Pull request scanning: Automatically checks dependencies in pull requests and opens fix PRs with required upgrades or patches
- Context-aware prioritization: Uses a dynamic risk score factoring in severity, reachability, exploit maturity, and business context
- One-click remediation: Generates customizable fix PRs to update vulnerable dependencies with minimal developer effort
- Continuous monitoring: Tracks changes in vulnerability databases and alerts you to newly disclosed issues in active projects
Related content: Read our guide to application security testing providers
Conclusion
Application security testing solutions are critical for detecting and mitigating vulnerabilities across the entire software development lifecycle. By combining SAST, DAST, IAST, and SCA, organizations can address different classes of risks, from insecure code to vulnerable dependencies and runtime misconfigurations.
Effective AST implementation not only improves software security posture but also reduces remediation costs by catching issues early. Selecting the right mix of tools tailored to your development environment and application architecture is key to building secure, resilient software systems.